Spring Special Limited Time 70% Discount Offer - Ends in 0d 00h 00m 00s - Coupon code = getmirror
Pass the Cisco Certified Specialist - Threat Hunting and Defending 300-220 Questions and answers with ExamsMirror
Exam 300-220 Premium Access
View all detail and faqs for the 300-220 exam
560 Students Passed
85% Average Score
90% Same Questions
A Cisco-focused SOC wants to move detection coverage higher on thePyramid of Pain. Which hunting outcome BEST supports this objective?
During a structured hunt, analysts using Cisco SIEM tools complete hypothesis testing and confirm malicious activity. What is the NEXT step in the Cisco threat hunting lifecycle?
A threat hunter is usingCisco Secure Network Analytics (Stealthwatch)to investigate possible lateral movement inside the network. Which behavior would MOST strongly indicate lateral movement using valid credentials?
A SOC using Cisco security technologies wants to measure the success of its threat hunting program over time. Which metric BEST reflects increased threat hunting maturity?
A security analyst receives an alert that host A, which has an IP address of 192.168.5.39, has a new browser extension installed. During an investigation of the SIEM tool logs, the analyst discovers that host A made continuous TCP connections to an IP address of 1.25.241.8 via TCP port 80. The 1.25.241.8 IP address is categorized as a C2 server. Which action should the analyst take to mitigate similar connections in the future?
A threat hunting team wants to ensure hunts are repeatable, scalable, and less dependent on individual analyst intuition. What is the MOST important process improvement?
Refer to the exhibit.
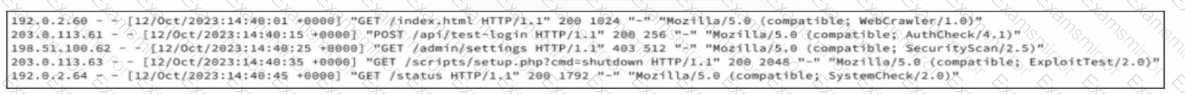
A company recently was breached and decided to improve their security posture going forward. A security assessment was ordered, specifically intended to test weak points exploited during the breach. A security analyst reviews server logs to identify activities related to the aforementioned security assessment. Which entry suggests a delivery method associated with authorized assessment?
A SOC analyst using Cisco security tools wants to differentiatethreat huntingfromtraditional detection engineering. Which activity BEST represents threat hunting rather than detection engineering?
A threat hunter usesCisco Secure Network Analytics (Stealthwatch)to identify potential command-and-control traffic. Which characteristic MOST strongly indicates beaconing behavior?
A mature SOC notices that several incidents over the past year involved attackers abusing legitimate administrative tools rather than deploying custom malware. Leadership asks the threat hunting team to improve detection coverage in a way that increases attacker cost rather than relying on easily replaceable indicators. Which detection strategy best aligns with this objective?
TOP CODES
Top selling exam codes in the certification world, popular, in demand and updated to help you pass on the first try.
