Spring Special Limited Time 70% Discount Offer - Ends in 0d 00h 00m 00s - Coupon code = getmirror
Pass the CrowdStrike CCFH CCFH-202b Questions and answers with ExamsMirror
Exam CCFH-202b Premium Access
View all detail and faqs for the CCFH-202b exam
360 Students Passed
97% Average Score
93% Same Questions
An attacker created a scheduled task which executes a remote management application. Which MITRE ATT & CK Matrix for Enterprise stage is this an example of?
Refer to the image.
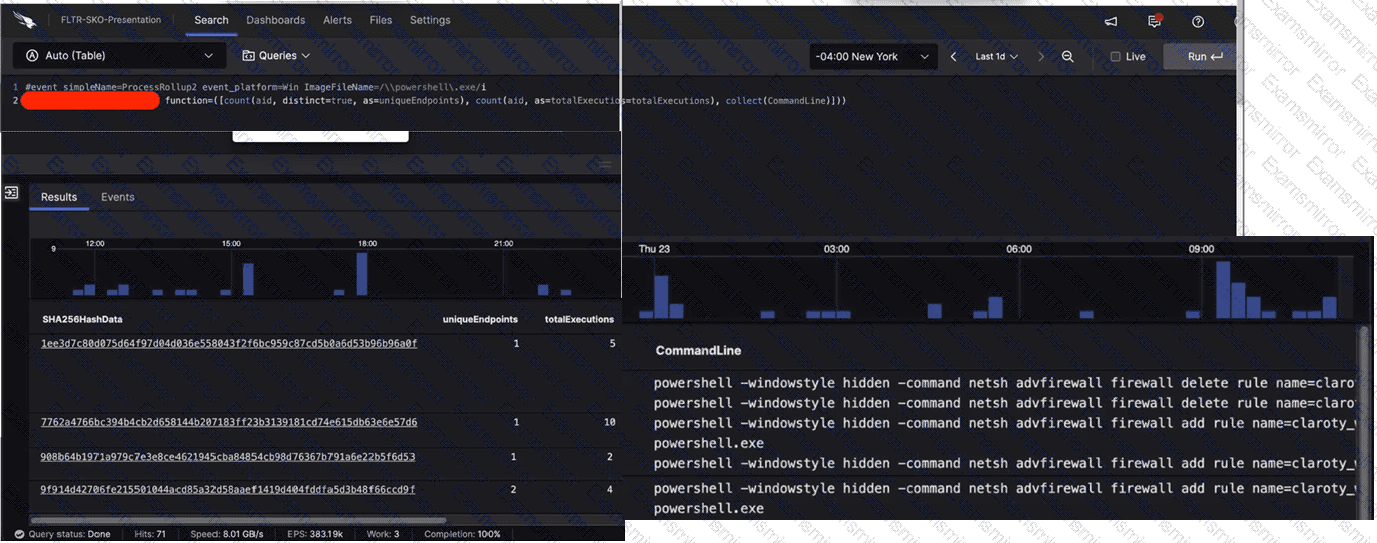
What aggregate function in the CrowdStrike Query Language (CQL) was used to provide the filtered results?
An independent investigation team based in Europe asks for the Event Search data to be formatted to Central European Summer Time (CEST). Which parameter within the formatTime() function is required to convert the Unix timestamps?
What is the purpose of this query?
#event_simpleName=UserLogon LogonType=10 RemoteAddressIP4=* | !cidr(RemoteAddressIP4, subnet=["224.0.0.0/4", "10.0.0.0/8", "172.16.0.0/12", "192.168.0.0/16", "127.0.0.0/8", "169.254.0.0/16", "0.0.0.0/32"]) | ipLocation(RemoteAddressIP4) | worldMap(ip=RemoteAddressIP4, magnitude=count(aid))
Which pre-defined reports will show activities that typically indicate suspicious activity occurring on a system?
Which CQL query would output relevant data in tracking USB storage device usage?
You are investigating a compromise on a Linux host. You suspect that the host is running an older version of Apache and that the Log4j (CVE-2021-44228) vulnerability is being exploited using JNDI lookups. Which CQL query could you use to determine if Log4j is the root cause of the compromise?
Which statement will filter for all events that correspond to a new scheduled task registered by the user "Doris"?
What can a hunter add at the end of a search string in Advanced Event Search to identify outliers when quantifying the results?
You've experienced a ransomware infection that has spread throughout the enterprise. What is the first step you would take to determine the source of infection?
TOP CODES
Top selling exam codes in the certification world, popular, in demand and updated to help you pass on the first try.
