Pre-Summer Special Limited Time 70% Discount Offer - Ends in 0d 00h 00m 00s - Coupon code = getmirror
Pass the Huawei HCIA-Datacom H12-811_V2.0 Questions and answers with ExamsMirror
Exam H12-811_V2.0 Premium Access
View all detail and faqs for the H12-811_V2.0 exam
343 Students Passed
94% Average Score
93% Same Questions
Both SNMP Trap and Inform Request are used by managed devices to send alarms to the NMS. Inform Request requires an acknowledgment from the NMS, whereas Trap does not.
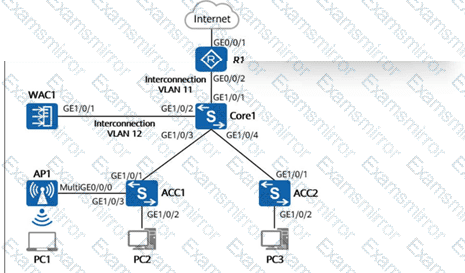
On the campus network shown in the figure below, the core switch Core1 functions as a Layer 3 gateway and as a DHCP server to dynamically assign IP addresses to AP1, PC1, PC2, and PC3. The network below Core1 is a Layer 2 network. WAC1 and R1 are connected to Core1 at Layer 3. AP1 goes online through VLAN 100. The wireless service VLAN is VLAN 101, and the wired service VLANs for PC2 and PC3 are VLAN 102 and VLAN 103, respectively. Additionally, the direct forwarding mode is used for wireless traffic forwarding. If no additional VLANs are allowed on device interfaces, which of the following VLANs must be allowed on GE1/0/1 of ACC1? (Select all that apply)
In Layer 3 in-path WLAN networking, the WAC and Fit APs are connected at Layer 3. APs can obtain the WAC’s address through broadcast or DHCP.
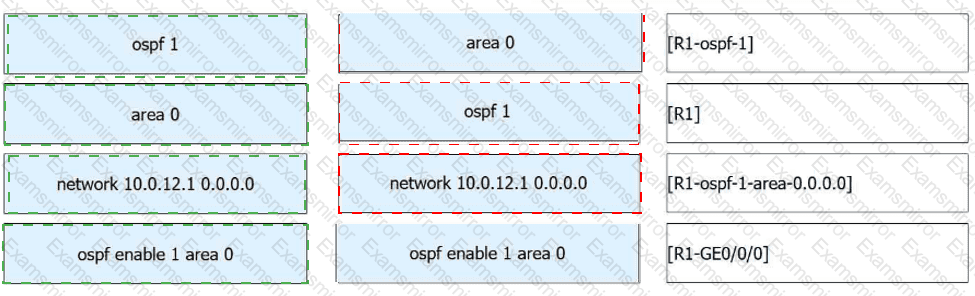
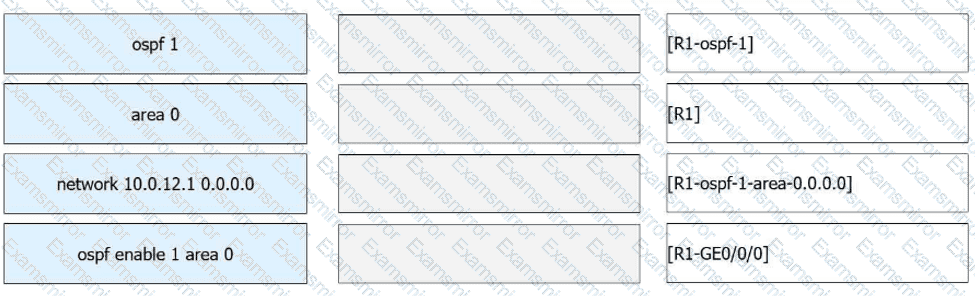
Assume that the IP address of GE0/0/0 on R1 is 10.0.12.1/24. Multiple commands can be used to enable OSPF on this interface. Match the commands with their configuration views.
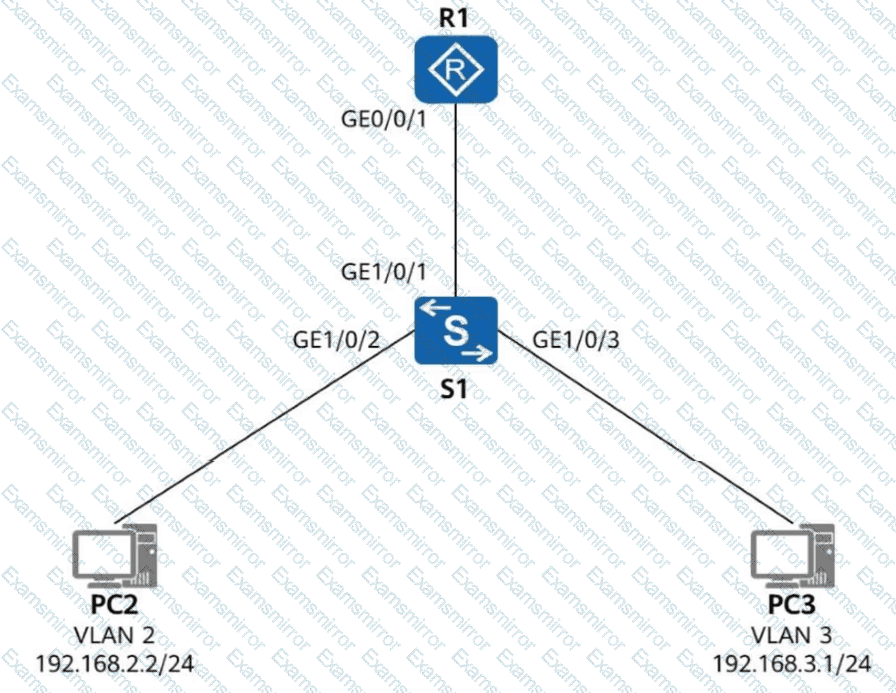
On the network shown in the figure, R1 serves as the gateway for PC2 and PC3, and directly connects to S1 through a physical link. GE1/0/1 on S1 is configured as a trunk interface and permits traffic of VLANs 2 and 3. Its PVID retains the default value. Which of the following statements are true if PC2 and PC3 can communicate with each other? (Select all that apply)
Secure Shell (SSH) is a protocol that uses encryption and authentication mechanisms to implement network services, such as secure access and file transfer, securely over an insecure network. Which of the following protocols use SSH? (Select all that apply)
In TCP/IP-based end-to-end communication, only the source and destination hosts process the header information added at the transport layer. Routers along the path will definitely not process this information.
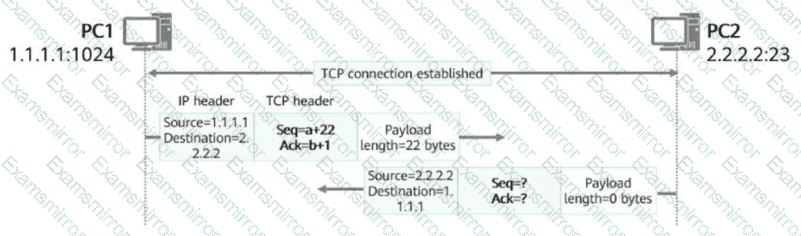
In the figure, a TCP connection has been established between PC1 and PC2. After PC1 sends a data segment to PC2, which of the following is the acknowledgment number in the packet returned by PC2?
OSPF has five types of packets. Which type is used to notify an OSPF neighbor of its required LSAs?
The following command output is displayed on R1:
[R1] display aaa configuration
Domain Name Delimiter : @
Domainname parse direction : Left to right
Domainname location : After-delimiter
Administrator user default domain : default_admin
Normal user default domain : default
Domain : total: 256 used: 3
Authentication-scheme : total: 32 used: 2
Accounting-scheme : total: 32 used: 1
Authorization-scheme : total: 32 used: 2
Service-scheme : total: 256 used: 0
Recording-scheme : total: 32 used: 0
Local-user : total: 512 used: 2
Remote-admin-user block retry-interval : 5 Min(s)
Remote-admin-user block retry-time : 3
Remote-admin-user block time : 5 Min(s)
Session timeout invalid enable : No
Which of the following statements is false?
TOP CODES
Top selling exam codes in the certification world, popular, in demand and updated to help you pass on the first try.