Spring Special Limited Time 70% Discount Offer - Ends in 0d 00h 00m 00s - Coupon code = getmirror
Pass the Juniper JNCIP-SEC JN0-636 Questions and answers with ExamsMirror
Exam JN0-636 Premium Access
View all detail and faqs for the JN0-636 exam
750 Students Passed
97% Average Score
95% Same Questions
In an effort to reduce client-server latency transparent mode was enabled an SRX series device.
Which two types of traffic will be permitted in this scenario? (Choose Two )
Exhibit
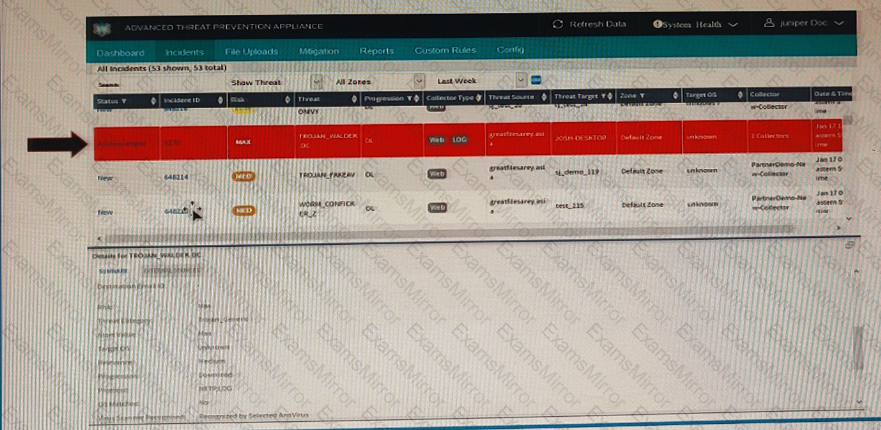
Exhibit.
Referring to the exhibit, which two statements are true? (Choose two.)
which security feature bypasses routing or switching lookup?
You are asked to determine if the 203.0.113.5 IP address has been added to the third-party security feed, DS hield, from Juniper Seclnte1. You have an SRX Series device that is using Seclnte1 feeds from Juniper ATP Cloud
Which command will return this information?
You are asked to configure a security policy on the SRX Series device. After committing the policy, you receive the “Policy is out of sync between RE and PFE
Which command would be used to solve the problem?
You opened a support ticket with JTAC for your Juniper ATP appliance. JTAC asks you to set up access to the device
using the reverse SSH connection.Which three setting must be configured to satisfy this request? (Choose three.)
You are requested to enroll an SRX Series device with Juniper ATP Cloud.
Which statement is correct in this scenario?
You are deploying a virtualization solution with the security devices in your network Each SRX Series device must support at least 100 virtualized instances and each virtualized instance must have its own discrete administrative domain.
In this scenario, which solution would you choose?
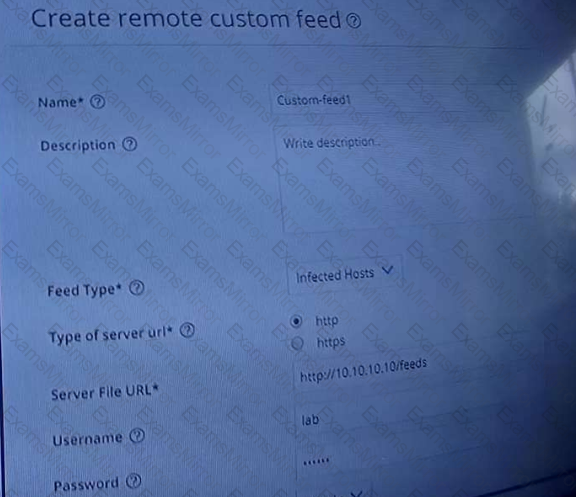
Exhibit
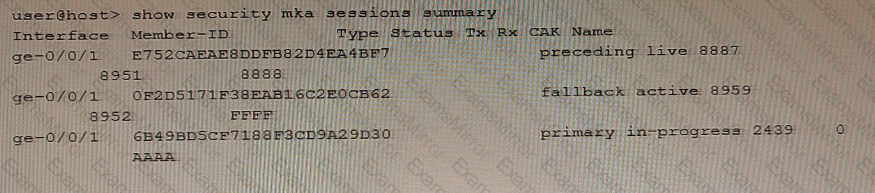
Referring to the exhibit, which two statements are true about the CAK status for the CAK named "FFFP"? (Choose two.)
TOP CODES
Top selling exam codes in the certification world, popular, in demand and updated to help you pass on the first try.
