Spring Special Limited Time 70% Discount Offer - Ends in 0d 00h 00m 00s - Coupon code = getmirror
Pass the Fortinet NSE 6 Network Security Specialist NSE6_OTS_AR-7.6 Questions and answers with ExamsMirror
Exam NSE6_OTS_AR-7.6 Premium Access
View all detail and faqs for the NSE6_OTS_AR-7.6 exam
688 Students Passed
88% Average Score
96% Same Questions
Refer to the exhibit.

A Logical Topology page of a FortiGate device is shown. Your OT company wants to gain visibility into the network. You decide to implement device detection with the Security Fabric. Based on the exhibit, which statement is correct? (Choose one answer)
Refer to the exhibit.
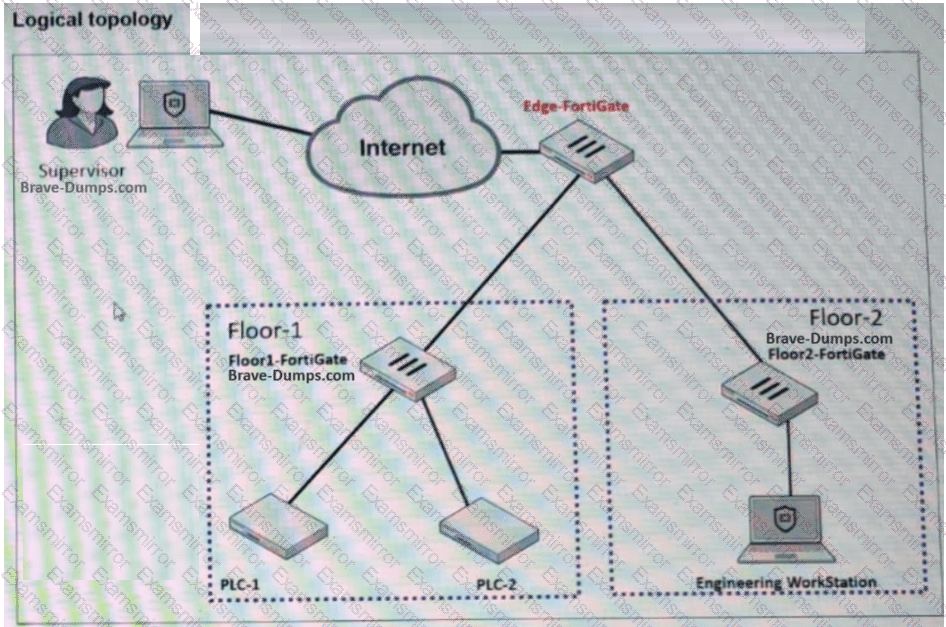
A partial OT network is shown. You want to provide the supervisor with secure remote access. Which two features can you implement on Edge-FortiGate ? (Choose two answers)
Refer to the exhibit.
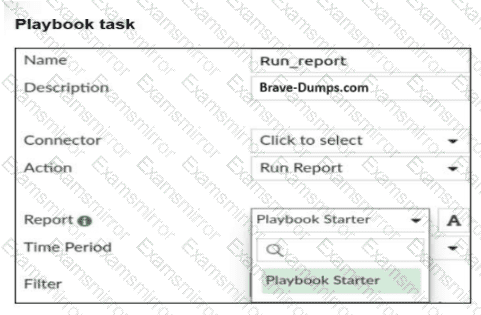
A Run_report task is shown. You want to automate the generation of a newly created report on FortiAnalyzer . When you configure the Run_report task in Playbook, why is the report not shown in the Report field? (Choose two answers)
Refer to the exhibit.
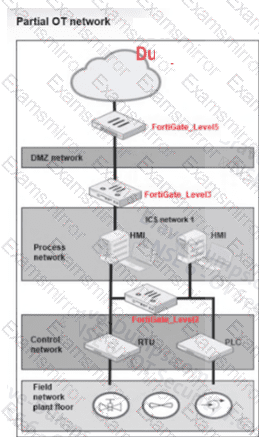
A partial OT network is shown. In this OT network, you must add additional security measures to detect OT protocols and, therefore, increase the traffic visibility. Which security sensor must you implement to detect the OT protocols in this network? (Choose one answer)
Refer to the exhibit.

A firewall policy page is shown. To improve the security of your OT network, you have configured a Supervisor profile in the firewall policies, as shown in the exhibit. However, a supervisor is reporting that he cannot ping PLC-1. What are the two reasons? (Choose two answers)
Refer to the exhibits.
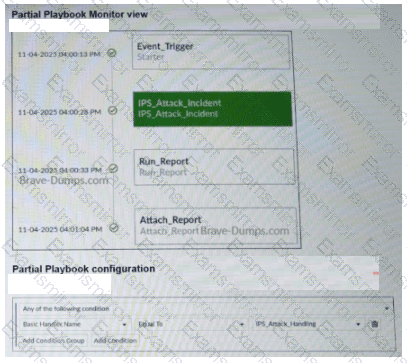
A partial view of the Playbook Monitor page and the corresponding playbook configuration are shown. Based on the monitor page and the configuration of the playbook, what has triggered the Run_Report task? (Choose one answer)
For the installation of your first FortiGate device, you want to minimize the impact in your OT network. Therefore, you deploy it initially as an offline IDS. Which two statements about this deployment are correct? (Choose two answers)
You want FortiAnalyzer to trigger an automation stitch on a FortiGate device automatically. What must you configure on FortiAnalyzer to enable direct communication with FortiGate? (Choose one answer)
According to the IEC 62443 standard, your security level is 4 . What is your OT environment defending against? (Choose one answer)
Refer to the exhibit.
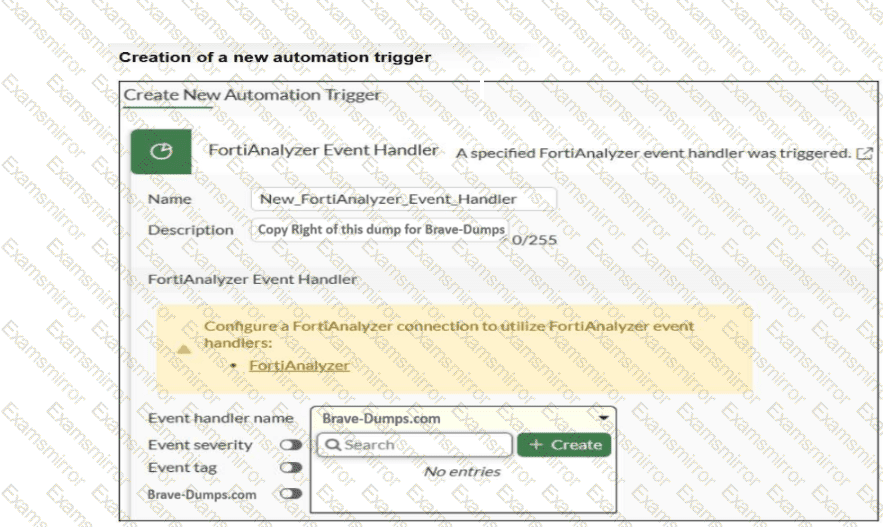
An automation trigger creation wizard is shown. You want to automate some tasks in your OT network. In a FortiGate device, you create a new automation trigger based on a FortiAnalyzer event handler. When you want to configure the Event handler name field, the event handler created in FortiAnalyzer is not shown. What are two reasons for this? (Choose two answers)
TOP CODES
Top selling exam codes in the certification world, popular, in demand and updated to help you pass on the first try.
