Spring Special Limited Time 70% Discount Offer - Ends in 0d 00h 00m 00s - Coupon code = getmirror
Pass the Fortinet Certified Professional Security Operations NSE7_SOC_AR-7.6 Questions and answers with ExamsMirror
Exam NSE7_SOC_AR-7.6 Premium Access
View all detail and faqs for the NSE7_SOC_AR-7.6 exam
504 Students Passed
97% Average Score
91% Same Questions
Refer to the exhibits.
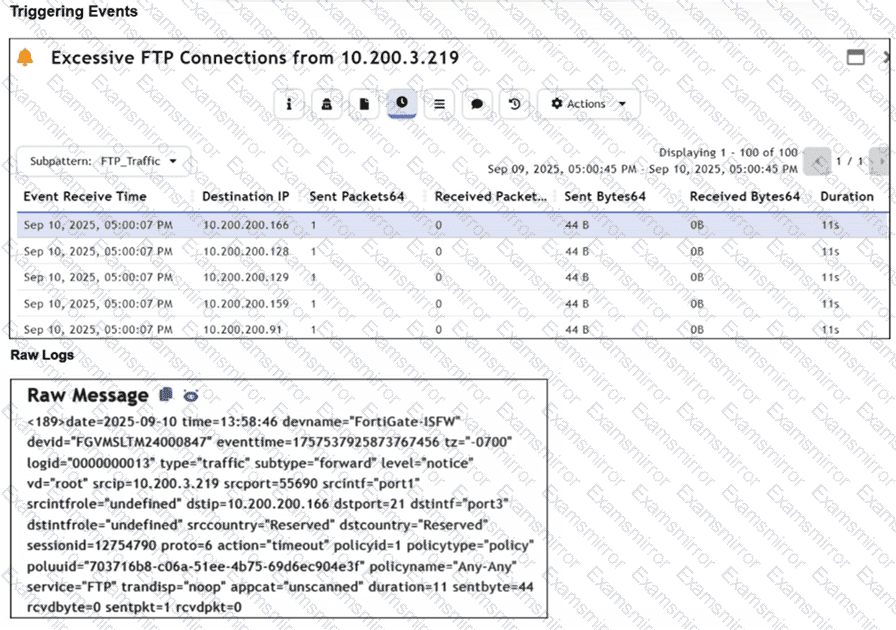
Assume that the traffic flows are identical, except for the destination IP address. There is only one FortiGate in network address translation (NAT) mode in this environment.
Based on the exhibits, which two conclusions can you make about this FortiSIEM incident? (Choose two answers)
Based on the Pyramid of Pain model, which two statements accurately describe the value of an indicator and how difficult it is for an adversary to change? (Choose two answers)
Exhibit:
Which observation about this FortiAnalyzer Fabric deployment architecture is true?
Which two ways can you create an incident on FortiAnalyzer? (Choose two.)
Which statement describes automation stitch integration between FortiGate and FortiAnalyzer?
Which three are threat hunting activities? (Choose three answers)
Which role does a threat hunter play within a SOC?
Which three end user logs does FortiAnalyzer use to identify possible IOC compromised hosts? (Choose three.)
Which FortiAnalyzer feature uses the SIEM database for advance log analytics and monitoring?
Refer to the exhibits.
The FortiMail Sender Blocklist playbook is configured to take manual input and add those entries to the FortiMail abc. com domain-level block list. The playbook is configured to use a FortiMail connector and the ADD_SENDER_TO_BLOCKLIST action.
Why is the FortiMail Sender Blocklist playbook execution failing7
TOP CODES
Top selling exam codes in the certification world, popular, in demand and updated to help you pass on the first try.
