Pre-Summer Special Limited Time 70% Discount Offer - Ends in 0d 00h 00m 00s - Coupon code = getmirror
Pass the GIAC Security Certification: GASF GCED Questions and answers with ExamsMirror
Exam GCED Premium Access
View all detail and faqs for the GCED exam
747 Students Passed
85% Average Score
90% Same Questions
Which statement below is the MOST accurate about insider threat controls?
If a Cisco router is configured with the “service config” configuration statement, which of the following tools could be used by an attacker to apply a new router configuration?
Which control would BEST help detect a potential insider threat?
On which layer of the OSI Reference Model does the FWSnort utility function?
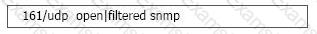
When running a Nmap UDP scan, what would the following output indicate?
You are responding to an incident involving a Windows server on your company’s network. During the investigation you notice that the system downloaded and installed two files, iexplorer.exe and iexplorer.sys. Based on the behavior of the system you suspect that these files are part of a rootkit. If this is the case what is the likely purpose of the .sys file?
Which of the following would be included in a router configuration standard?
Which tool uses a Snort rules file for input and by design triggers Snort alerts?
When an IDS system looks for a pattern indicating a known worm, what type of detection method is it using?
Why would an incident handler acquire memory on a system being investigated?
TOP CODES
Top selling exam codes in the certification world, popular, in demand and updated to help you pass on the first try.
