Pre-Summer Special Limited Time 70% Discount Offer - Ends in 0d 00h 00m 00s - Coupon code = getmirror
Pass the GIAC Certification GCFW Questions and answers with ExamsMirror
Exam GCFW Premium Access
View all detail and faqs for the GCFW exam
860 Students Passed
85% Average Score
97% Same Questions
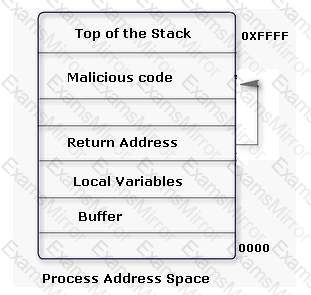
An attacker changes the address of a sub-routine in such a manner that it begins to point to the address of the malicious code. As a result, when the function has been exited, the application can be forced to shift to the malicious code. The image given below explains this phenomenon:
Which of the following tools can be used as a countermeasure to such an attack?
Which of the following tools can be used as a Linux vulnerability scanner that is capable of identifying operating systems and network services?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following types of audit constructs a risk profile for existing and new projects?
A remote-access VPN offers secured and encrypted connections between mobile or remote users and their corporate network across public networks. Which of the following does the remote-access VPN use for offering these types of connections?
Each correct answer represents a complete solution. Choose two.
John works as a professional Ethical Hacker. He has been assigned the project of testing the security of www.we-are-secure.com. In order to do so, he performs the following steps of the preattack phase successfully:
l Information gathering
l Determination of network range
l Identification of active systems
l Location of open ports and applications
Now, which of the following tasks should he perform next?
John works as a professional Ethical Hacker. He has been assigned the project of testing the security of www.we-are-secure.com. He has successfully performed the following steps of the pre-attack phase to check the security of the We-are-secure network:
l Gathering information
l Determining the network range
l Identifying active systems
Now, he wants to find the open ports and applications running on the network. Which of the following tools will he use to accomplish his task?
Which of the following Intrusion Detection Systems (IDS) is used to monitor rogue access points and the use of wireless attack tools?
Which of the following intrusion detection systems (IDS) produces the false alarm because of the abnormal behavior of users and network?
Which of the following IPv4 to IPv6 transition methods uses encapsulation of IPv6 packets to traverse IPv4 networks?
Which of the following firewall types operates at the Network layer of the OSI model and can filter data by port, interface address, source address, and destination address?
TOP CODES
Top selling exam codes in the certification world, popular, in demand and updated to help you pass on the first try.
