Pre-Summer Special Limited Time 70% Discount Offer - Ends in 0d 00h 00m 00s - Coupon code = getmirror
Pass the Citrix CCE-N 1Y0-440 Questions and answers with ExamsMirror
Exam 1Y0-440 Premium Access
View all detail and faqs for the 1Y0-440 exam
838 Students Passed
85% Average Score
98% Same Questions
Scenario: A Citrix Architect needs to plan for a customer environment in which more than 10,000 users will need access. The networking infrastructure needs to be able to handle the expected usage.
Which business driver should be prioritized based on the customer’s requirement?
Scenario: A Citrix Architect needs to deploy SAML integration between NetScaler (Identity Provider) and ShareFile (Service Provider). The design requirements for SAML setup are as follows:
NetScaler must be deployed as the Identity Provider (IDP).
ShareFile server must be deployed as the SAML Service Provider (SP).
The users in domain workspacelab.com must be able to perform Single Sign-on to ShareFile after authenticating at the NetScaler.
The User ID must be UserPrincipalName.
The User ID and Password must be evaluated by NetScaler against the Active Directory servers SFO-ADS-001 and SFO-ADS-002.
After successful authentication, NetScaler creates a SAML Assertion and passes it back to ShareFile.
Single Sign-on must be performed.
SHA 1 algorithm must be utilized.
The verification environment details are as follows:
Domain Name: workspacelab.com
NetScaler AAA virtual server URL https://auth.workspacelab.com
ShareFile URL https://sharefile.workspacelab.com
Which SAML IDP action will meet the design requirements?
Which parameter indicates the number of current users logged on to the Citrix gateway?
Scenario: The Workspacelab team has implemented Citrix ADC high availability pair and Citrix ADC Management and Analytics System (Citrix Application Delivery Management). The Citrix Application Delivery Management was configured by a Citrix Architect to monitor and manage these devices. The Workspacelab team wants to load balance their Microsoft SharePoint servers on the Citrix ADC and needs the process to be streamlined and administered using Citrix Application Delivery Management.
The following requirements were discussed during the meeting:
The Microsoft SharePoint server should be optimized, load balanced, and secured in the network and should be deployed using Citrix Application Delivery Management.
All the configurations should be yenned before getting pushed to the Citrix Application Delivery Management.
Which feature should the architect use to configure the Microsoft SharePoint server using Citrix Application Delivery Management?
Which statement is applicable to Citrix Gateway split tunneling?
Scenario: A Citrix Architect has sent the following request to the NetScaler:
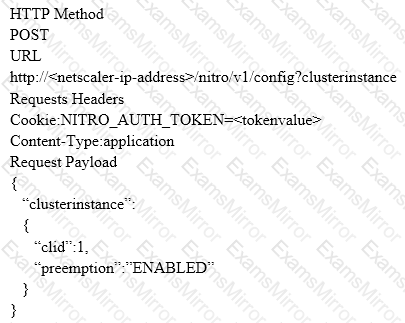
Which response would indicate the successful execution of the NITRO command?
Scenario: A Citrix Architect has setup Citrix ADC MPX devices in high availability mode with version 12.0.53.13 nc. These are placed behind a Cisco ASA 5505 firewall. The Cisco ASA firewall is configured to block traffic using access control lists. The network address translation (NAT) is also performed on the firewall. The following requirements were captured by the architect during the discussion held as part of the Citrix ADC security implementation project with the customer's security team: The Citrix ADC MPX device:
should monitor the rate of traffic either on a specific virtual entity or on the device. It should be able to mitigate the attacks from a hostile client sending a flood of requests. The Citrix ADC device should be able to stop the HTTP. TOP, and DNS based requests.
needs to protect backend servers from overloading.
needs to queue all the incoming requests on the virtual server level instead of the service level.
should provide access to resources on the basis of priority.
should provide protection against well-known Windows exploits, virus-infected personal computers, centrally managed automated botnets. compromised webservers, known spammersThackers. and phishing proxies.
should provide flexibility to enforce the desired level of security check inspections for the requests originating from a specific geolocation database.
should block the traffic based on a predetermined header length, URL length, and cookie length.The device should ensure that characters such as a single straight quote (') backslash (); and semicolon (;) are either blocked, transformed, or dropped while being sent to the backend server.
Which security feature should the architect implement to meet these requirements?
Which markup language can a Citrix use along with NITRO API to create a StyleBook?
Scenario: A Citrix Architect needs to assess an existing NetScaler gateway deployment. During the assessment, the architect collected key requirements for VPN users, as well as the current session profile settings that are applied to those users.
Click the Exhibit button to view the information collected by the architect.
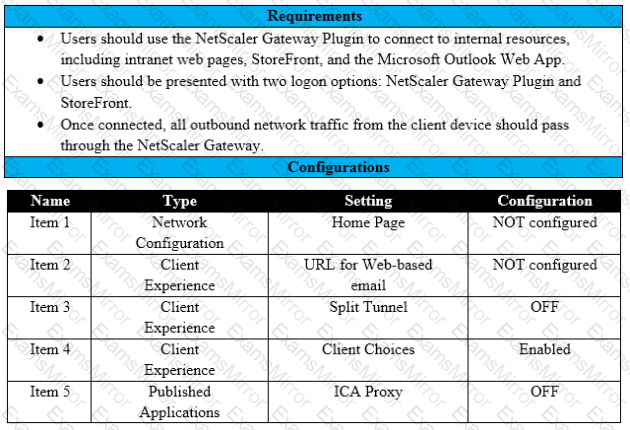
Which configuration should the architect change to meet all the stated requirements?
Scenario: A Citrix Architect holds a design discussion with a team of Workspacelab members, and they capture the following requirements for the Citrix ADC design project:
A pair of Citrlx ADC MPX appliances will be deployed in the DMZ network and another pair in the internal network.
High availability will be accessible between the pair of Citrix ADC MPX appliances in the DMZ network.
Multi-factor authentication must be configured for the Citrix Gateway virtual server.
The Citrix Gateway virtual server is integrated with the StoreFront server.
Load balancing must be configured for the StoreFront server. •Authentication must be deployed for users from the workspacelab.com domain.
The Workspacelab users should be authenticated using Cert Policy and LDAP.
All the client certificates must be SHA 256-signed, 2048 bits, and have UserPrincipalName as the subject.
Single Sign-on must be performed between StoreFront and Citrix Gateway. After deployment the architect observes that LDAP authentication is failing.
Click the Exhibit button to review the output of aaad.debug and the configuration of the authentication policy.
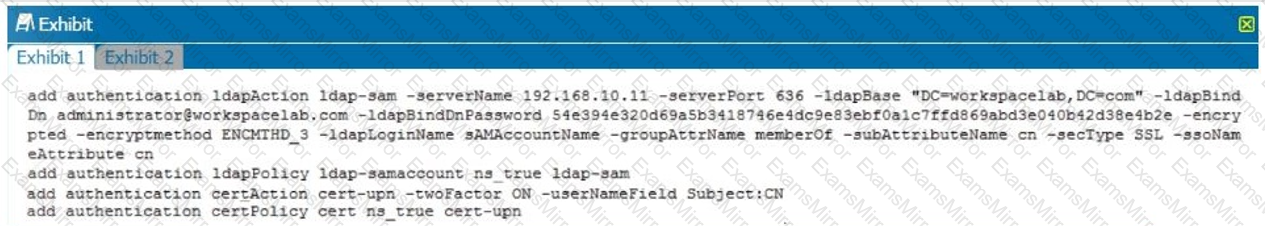
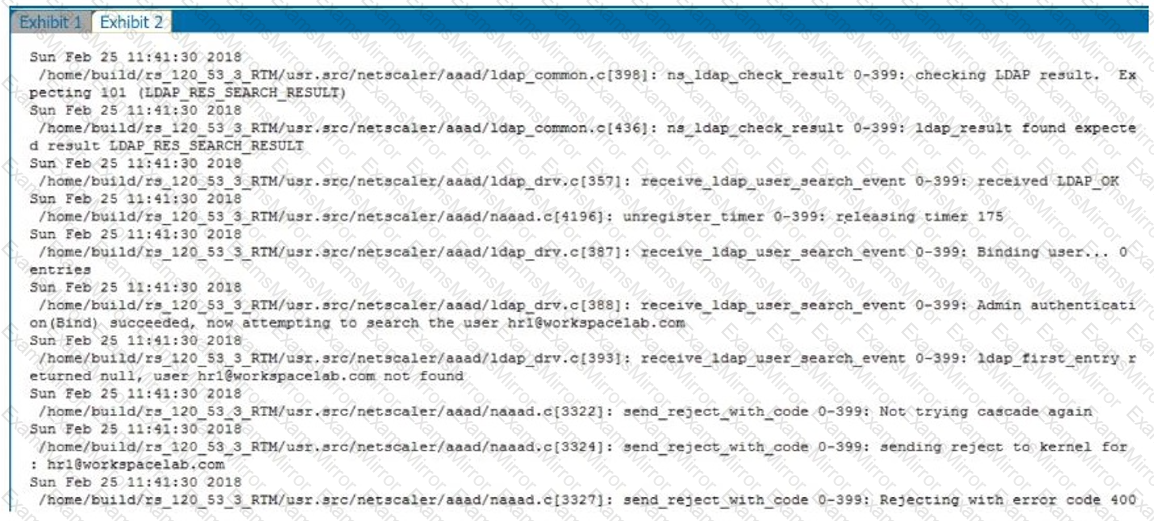
What is causing this issue?
TOP CODES
Top selling exam codes in the certification world, popular, in demand and updated to help you pass on the first try.
