Pre-Summer Special Limited Time 70% Discount Offer - Ends in 0d 00h 00m 00s - Coupon code = getmirror
Pass the GAQM Information Systems Security CPEH-001 Questions and answers with ExamsMirror
Exam CPEH-001 Premium Access
View all detail and faqs for the CPEH-001 exam
697 Students Passed
84% Average Score
91% Same Questions
What is one of the advantages of using both symmetric and asymmetric cryptography in SSL/TLS?
Which of the following attacks exploits web age vulnerabilities that allow an attacker to force an unsuspecting user’s browser to send malicious requests they did not intend?
What would you enter, if you wanted to perform a stealth scan using Nmap?
In which of the following cryptography attack methods, the attacker makes a series of interactive queries, choosing subsequent plaintexts based on the information from the previous encryptions?
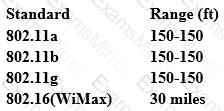
From the following table, identify the wrong answer in terms of Range (ft).
What is the minimum number of network connections in a multi homed firewall?
Which one of the following Google advanced search operators allows an attacker to restrict the results to those websites in the given domain?
Which of the following is the best countermeasure to encrypting ransomwares?
During a blackbox pen test you attempt to pass IRC traffic over port 80/TCP from a compromised web enabled host. The traffic gets blocked; however, outbound HTTP traffic is unimpeded.
What type of firewall is inspecting outbound traffic?
You are logged in as a local admin on a Windows 7 system and you need to launch the Computer Management Console from command line.
Which command would you use?
You are performing information gathering for an important penetration test. You have found pdf, doc, and images in your objective. You decide to extract metadata from these files and analyze it.
What tool will help you with the task?
An attacker has installed a RAT on a host. The attacker wants to ensure that when a user attempts to go to "www.MyPersonalBank.com ", that the user is directed to a phishing site.
Which file does the attacker need to modify?
You are performing a penetration test. You achieved access via a buffer overflow exploit and you proceed to find interesting data, such as files with usernames and passwords. You find a hidden folder that has the administrator's bank account password and login information for the administrator's bitcoin account.
What should you do?
Which of the following is the structure designed to verify and authenticate the identity of individuals within the enterprise taking part in a data exchange?
Which of the following is a component of a risk assessment?
TOP CODES
Top selling exam codes in the certification world, popular, in demand and updated to help you pass on the first try.
