Pre-Summer Special Limited Time 70% Discount Offer - Ends in 0d 00h 00m 00s - Coupon code = getmirror
Pass the GIAC Audit GSNA GSNA Questions and answers with ExamsMirror
Exam GSNA Premium Access
View all detail and faqs for the GSNA exam
741 Students Passed
93% Average Score
97% Same Questions
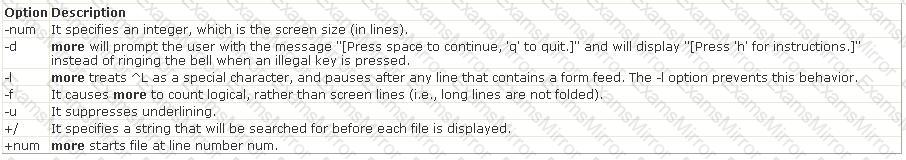
You want to change the number of characters displaying on the screen while reading a txt file. However, you do not want to change the format of the txt file. Which of the following commands can be used to view (but not modify) the contents of the text file on the terminal screen at a time?
You work as a Network Administrator for NTY Inc. The company has a secure wireless network. While auditing the network for maintaining security, you find an unknown node. You want to locate that node. Which tool will you use to pinpoint the actual physical location of the node?
You work as a Network Administrator for Tech Perfect Inc. The company has a TCP/IP-based network. You have configured a firewall on the network. A filter has been applied to block all the ports. You want to enable sending and receiving of emails on the network. Which of the following ports will you open? (Choose two)
What is the purpose of Cellpadding attribute of

 C:\Documents and Settings\user-nwz\Desktop\1.JPG
C:\Documents and Settings\user-nwz\Desktop\1.JPG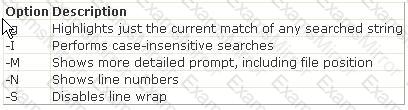 C:\Documents and Settings\user-nwz\Desktop\1.JPG
C:\Documents and Settings\user-nwz\Desktop\1.JPG