Pre-Summer Special Limited Time 70% Discount Offer - Ends in 0d 00h 00m 00s - Coupon code = getmirror
Pass the Logical Operations CyberSec First Responder CFR-210 Questions and answers with ExamsMirror
Exam CFR-210 Premium Access
View all detail and faqs for the CFR-210 exam
807 Students Passed
96% Average Score
91% Same Questions
To redact or obfuscate sensitive data, a company requires its name be changed throughout a port-incident report. Using a Linux sed command, which of the following will replace the company’s name with “Acme”?
A logfile generated from a Windows server was moved to a Linux system for further analysis. A system administrator is now making edits to the file with vi and notices the file contains numerous instances of Ctrl-M (^M) characters. Which of the following command line tools is the administrator MOST likely to use to remove these characters from the logfile? (Choose two.)
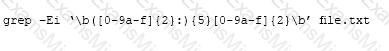
The above Linux command is used to search for:
An attacker has decided to attempt a brute force attack on a UNIX server. In order to accomplish this, which of the following steps must be performed?
Which of the following commands should be used to print out ONLY the second column of items in the following file?
Source_File,txt
Alpha Whiskey
Bravo Tango
Charlie Foxtrot
Echo Oscar
Delta Roger
When performing an investigation, a security analyst needs to extract information from text files in a Windows operating system. Which of the following commands should the security analyst use?
A UNIX workstation has been compromised. The security analyst discovers high CPU usage during off-hours on the workstation. Which of the following UNIX programs can be used to detect the rogue process? (Choose two.)
The Chief Information Officer (CIO) of a company asks the incident responder to update the risk management plan. Which of the following methods can BEST help the incident responder identify the risks that require in-depth analysis?
A hacker’s end goal is to target the Chief Financial Officer (CFO) of a bank. Which of the following describes this social engineering tactic?
While performing standard maintenance on a UNIX server, a system administrator notices a set of large files with .tar .gz file extensions in the /tmp folder. The system administrator reports this to a security analyst. Performing further research, the analyst has found the .tar .gz files contain information normally housed on one of the bank’s data servers. Given this scenario, which of the following is MOST likely occurring?
TOP CODES
Top selling exam codes in the certification world, popular, in demand and updated to help you pass on the first try.
