Pre-Summer Special Limited Time 70% Discount Offer - Ends in 0d 00h 00m 00s - Coupon code = getmirror
Pass the Logical Operations CyberSec First Responder CFR-210 Questions and answers with ExamsMirror
Exam CFR-210 Premium Access
View all detail and faqs for the CFR-210 exam
807 Students Passed
96% Average Score
91% Same Questions
During review of a company’s web server logs, the following items are discovered:
2015-03-01 03:32:11 www.example.com/index.asp?id=-999 or 1=convert(int,@@version)—
2015-03-01 03:35:33 www.example.com/index.asp?id=-999 or 1=convert(int,db_name())—
2015-03-01 03:38:25 www.example.com/index.asp?id=-999 or 1=convert(int,user_name())—
Which of the following is depicted in the log example above?
During the course of an investigation, an incident responder discovers illegal material on a user’s hard drive. Which of the following is the incident responder’s MOST important next step?
An incident responder is investigating a Linux server reported to be “behaving strangely”. Which of the following commands should the incident responder use to identify any users currently logged into the system? (Choose two.)
A malicious attacker has compromised a database by implementing a Python-based script that will automatically establish an SSH connection daily between the hours of 2:00 am and 5:00 am. Which of the following is the MOST common motive for the attack vector that was used?
A DMZ web server has been compromised. During the log review, the incident responder wants to parse all common internal Class A addresses from the log. Which of the following commands should the responder use to accomplish this?
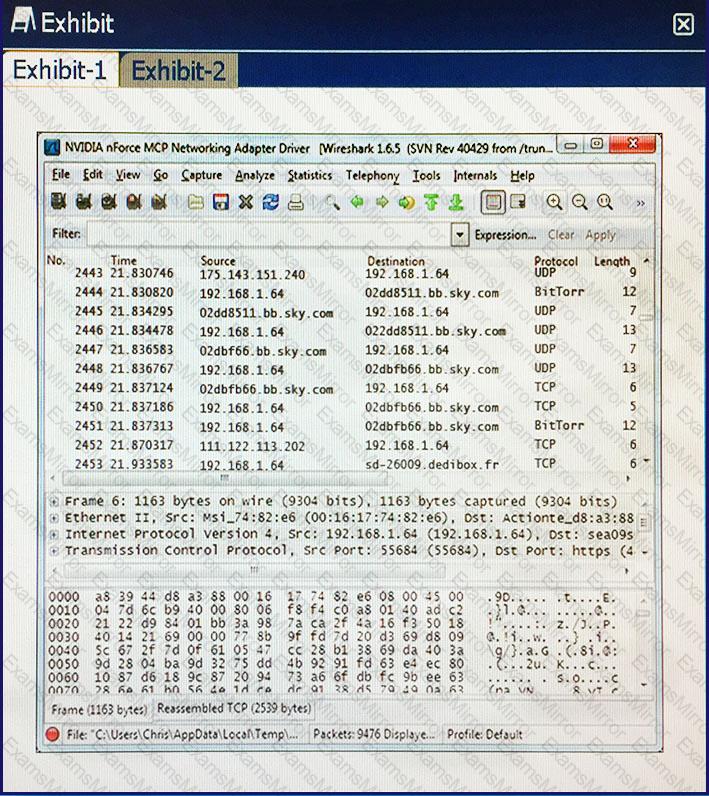
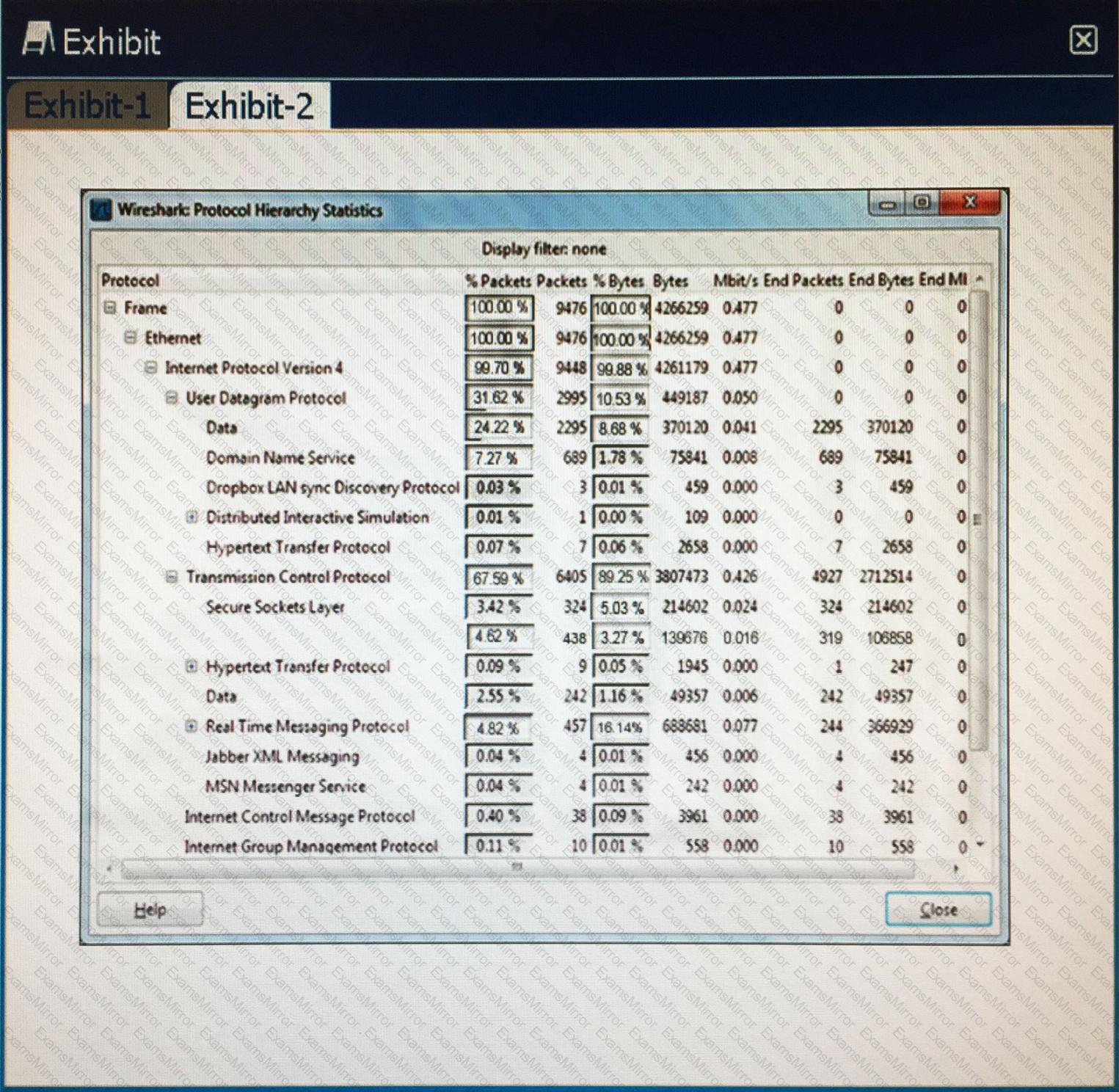
Click the exhibit button. After reviewing captured network traffic logs, a security auditor suspects a violation of the organization’s computer use policy. Which of the following is the likely indicator of the violation?
A computer attacker has compromised a system by implanting a script that will send 10B packages over port 150. This port is also used for sending heartbeat messages to a central monitoring server. Which of the following BEST describes the tactic used to execute this attack?
Organizations should exercise their Incident Response (IR) plan following initial creation. The primary objective for this first IR plan exercise is to identify:
Which of the following logs should be checked to determine if an internal user connected to a potentially malicious website? (Choose two.)
A zero-day vulnerability is discovered on a company’s network. The security analyst conducts a log review, schedules an immediate vulnerability scan, and quarantines the infected system, but cannot determine the root cause of the vulnerability. Which of the following is a source of information that can be used to identify the cause of the vulnerability?
TOP CODES
Top selling exam codes in the certification world, popular, in demand and updated to help you pass on the first try.
