Pre-Summer Special Limited Time 70% Discount Offer - Ends in 0d 00h 00m 00s - Coupon code = getmirror
Pass the GAQM Certified Ethical Hacker CEH CEH-001 Questions and answers with ExamsMirror
Exam CEH-001 Premium Access
View all detail and faqs for the CEH-001 exam
796 Students Passed
86% Average Score
93% Same Questions
A zone file consists of which of the following Resource Records (RRs)?
Exhibit:
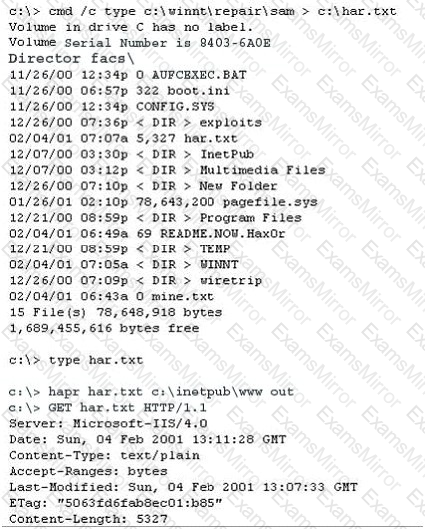
Based on the following extract from the log of a compromised machine, what is the hacker really trying to steal?
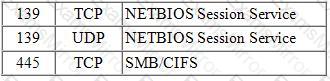
Null sessions are un-authenticated connections (not using a username or password.) to an NT or 2000 system. Which TCP and UDP ports must you filter to check null sessions on your network?
Which definition among those given below best describes a covert channel?
You have the SOA presented below in your Zone. Your secondary servers have not been able to contact your primary server to synchronize information. How long will the secondary servers attempt to contact the primary server before it considers that zone is dead and stops responding to queries?
collegae.edu.SOA, cikkye.edu ipad.college.edu. (200302028 3600 3600 604800 3600)
Sandra is the security administrator of XYZ.com. One day she notices that the XYZ.com Oracle database server has been compromised and customer information along with financial data has been stolen. The financial loss will be estimated in millions of dollars if the database gets into the hands of competitors. Sandra wants to report this crime to the law enforcement agencies immediately.
Which organization coordinates computer crime investigations throughout the United States?
Your XYZ trainee Sandra asks you which are the four existing Regional Internet Registry (RIR's)?
Your lab partner is trying to find out more information about a competitors web site. The site has a .com extension. She has decided to use some online whois tools and look in one of the regional Internet registrys. Which one would you suggest she looks in first?
You have initiated an active operating system fingerprinting attempt with nmap against a target system:
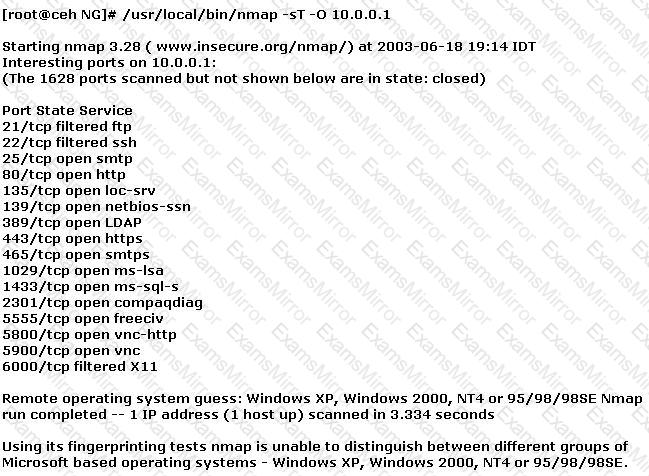
What operating system is the target host running based on the open ports shown above?
What ICMP message types are used by the ping command?
A company is legally liable for the content of email that is sent from its systems, regardless of whether the message was sent for private or business-related purposes. This could lead to prosecution for the sender and for the company's directors if, for example, outgoing email was found to contain material that was pornographic, racist, or likely to incite someone to commit an act of terrorism. You can always defend yourself by "ignorance of the law" clause.
What is the following command used for?
net use \targetipc$ "" /u:""
While performing ping scans into a target network you get a frantic call from the organization’s security team. They report that they are under a denial of service attack. When you stop your scan, the smurf attack event stops showing up on the organization’s IDS monitor. How can you modify your scan to prevent triggering this event in the IDS?
To what does “message repudiation” refer to what concept in the realm of email security?
A distributed port scan operates by:
Which Windows system tool checks integrity of critical files that has been digitally signed by Microsoft?
Which type of Nmap scan is the most reliable, but also the most visible, and likely to be picked up by and IDS?
You are manually conducting Idle Scanning using Hping2. During your scanning you notice that almost every query increments the IPID regardless of the port being queried. One or two of the queries cause the IPID to increment by more than one value. Why do you think this occurs?
Which of the following systems would not respond correctly to an nmap XMAS scan?
Who is an Ethical Hacker?
TOP CODES
Top selling exam codes in the certification world, popular, in demand and updated to help you pass on the first try.

 C:\Documents and Settings\user-nwz\Desktop\1.JPG
C:\Documents and Settings\user-nwz\Desktop\1.JPG