Pre-Summer Special Limited Time 70% Discount Offer - Ends in 0d 00h 00m 00s - Coupon code = getmirror
Pass the GAQM Certified Ethical Hacker CEH CEH-001 Questions and answers with ExamsMirror
Exam CEH-001 Premium Access
View all detail and faqs for the CEH-001 exam
796 Students Passed
86% Average Score
93% Same Questions
Which of the following is a protocol that is prone to a man-in-the-middle (MITM) attack and maps a 32-bit address to a 48-bit address?
Bluetooth uses which digital modulation technique to exchange information between paired devices?
To send a PGP encrypted message, which piece of information from the recipient must the sender have before encrypting the message?
Smart cards use which protocol to transfer the certificate in a secure manner?
What is the outcome of the comm”nc -l -p 2222 | nc 10.1.0.43 1234"?
Which command line switch would be used in NMAP to perform operating system detection?
Which of the following ensures that updates to policies, procedures, and configurations are made in a controlled and documented fashion?
While testing the company's web applications, a tester attempts to insert the following test script into the search area on the company's web sitE.
<script>alert(" Testing Testing Testing ")</script>
Afterwards, when the tester presses the search button, a pop-up box appears on the screen with the text: "Testing Testing Testing". Which vulnerability has been detected in the web application?
When using Wireshark to acquire packet capture on a network, which device would enable the capture of all traffic on the wire?
How do employers protect assets with security policies pertaining to employee surveillance activities?
The intrusion detection system at a software development company suddenly generates multiple alerts regarding attacks against the company's external webserver, VPN concentrator, and DNS servers. What should the security team do to determine which alerts to check first?
Which of the following is a detective control?
A security administrator notices that the log file of the company`s webserver contains suspicious entries:
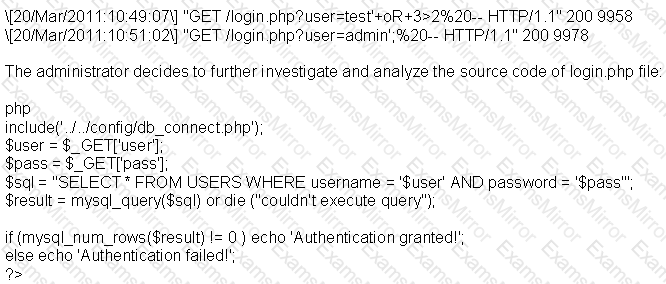
Based on source code analysis, the analyst concludes that the login.php script is vulnerable to
When analyzing the IDS logs, the system administrator noticed an alert was logged when the external router was accessed from the administrator's computer to update the router configuration. What type of an alert is this?
What is the most secure way to mitigate the theft of corporate information from a laptop that was left in a hotel room?
What type of OS fingerprinting technique sends specially crafted packets to the remote OS and analyzes the received response?
A security policy will be more accepted by employees if it is consistent and has the support of
What is a successful method for protecting a router from potential smurf attacks?
Which of the following is an example of IP spoofing?
How can rainbow tables be defeated?
TOP CODES
Top selling exam codes in the certification world, popular, in demand and updated to help you pass on the first try.
