Pre-Summer Special Limited Time 70% Discount Offer - Ends in 0d 00h 00m 00s - Coupon code = getmirror
Pass the GAQM Certified Ethical Hacker CEH CEH-001 Questions and answers with ExamsMirror
Exam CEH-001 Premium Access
View all detail and faqs for the CEH-001 exam
796 Students Passed
86% Average Score
93% Same Questions
Which type of attack is port scanning?
Exhibit:
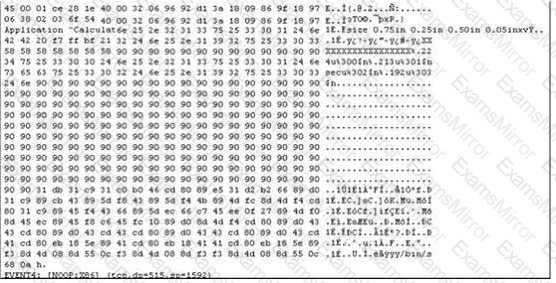
The following is an entry captured by a network IDS.You are assigned the task of analyzing this entry. You notice the value 0x90, which is the most common NOOP instruction for the Intel processor. You figure that the attacker is attempting a buffer overflow attack. You also notice "/bin/sh" in the ASCII part of the output. As an analyst what would you conclude about the attack?
Password cracking programs reverse the hashing process to recover passwords.(True/False.
How can you determine if an LM hash you extracted contains a password that is less than 8 characters long?
Which of the following is the primary objective of a rootkit?
Eric has discovered a fantastic package of tools named Dsniff on the Internet. He has learnt to use these tools in his lab and is now ready for real world exploitation. He was able to effectively intercept communications between the two entities and establish credentials with both sides of the connections. The two remote ends of the communication never notice that Eric is relaying the information between the two.
What would you call this attack?
Which of the following Netcat commands would be used to perform a UDP scan of the lower 1024 ports?
What is the algorithm used by LM for Windows2000 SAM?
What hacking attack is challenge/response authentication used to prevent?
Study the snort rule given below:
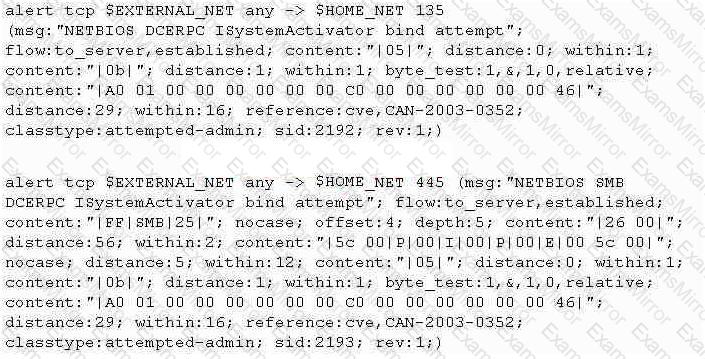
From the options below, choose the exploit against which this rule applies.
What happens when one experiences a ping of death?
Peter, a Network Administrator, has come to you looking for advice on a tool that would help him perform SNMP enquires over the network. Which of these tools would do the SNMP enumeration he is looking for?
Select the best answers.
Eve is spending her day scanning the library computers. She notices that Alice is using a computer whose port 445 is active and listening. Eve uses the ENUM tool to enumerate Alice machine. From the command prompt, she types the following command.
For /f "tokens=1 %%a in (hackfile.txt) do net use * \\10.1.2.3\c$ /user:"Administrator" %%a
What is Eve trying to do?
Tess King is using the nslookup command to craft queries to list all DNS information (such as Name Servers, host names, MX records, CNAME records, glue records (delegation for child Domains), zone serial number, TimeToLive (TTL) records, etc) for a Domain. What do you think Tess King is trying to accomplish? Select the best answer.
You suspect that your Windows machine has been compromised with a Trojan virus. When you run anti-virus software it does not pick of the Trojan. Next you run netstat command to look for open ports and you notice a strange port 6666 open.
What is the next step you would do?
Which of the following keyloggers cannot be detected by anti-virus or anti-spyware products?
Exhibit:
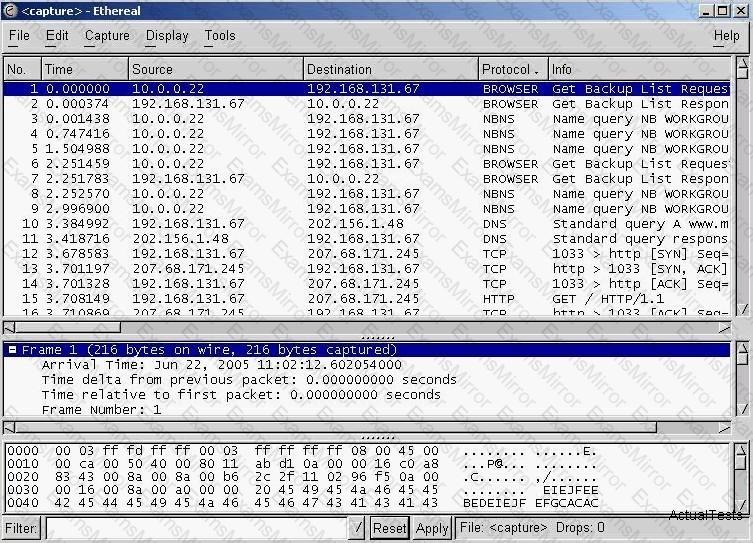
You have captured some packets in Ethereal. You want to view only packets sent from 10.0.0.22. What filter will you apply?
One of your junior administrator is concerned with Windows LM hashes and password cracking. In your discussion with them, which of the following are true statements that you would point out?
Select the best answers.
Fingerprinting an Operating System helps a cracker because:
When discussing passwords, what is considered a brute force attack?
TOP CODES
Top selling exam codes in the certification world, popular, in demand and updated to help you pass on the first try.
