Pre-Summer Special Limited Time 70% Discount Offer - Ends in 0d 00h 00m 00s - Coupon code = getmirror
Pass the GIAC Security Administration GPEN Questions and answers with ExamsMirror
Exam GPEN Premium Access
View all detail and faqs for the GPEN exam
742 Students Passed
93% Average Score
92% Same Questions
John works as a professional Ethical Hacker. He has been assigned the project of testing the security of www.we-are-secure.com. He has successfully performed the following steps of the preattack phase to check the security of the We-are-secure network:
l Gathering information
l Determining the network range
l Identifying active systems
Now, he wants to find the open ports and applications running on the network. Which of the following tools will he use to accomplish his task?
Ryan wants to create an ad hoc wireless network so that he can share some important files with another employee of his company. Which of the following wireless security protocols should he choose for setting up an ad hoc wireless network?
Each correct answer represents a part of the solution. Choose two.
Which of the following is a tool for SSH and SSL MITM attacks?
You want to create a binary log file using tcpdump. Which of the following commands will you use?
You configure a wireless router at your home. To secure your home Wireless LAN (WLAN), you implement WEP. Now you want to connect your client computer to the WLAN. Which of the following is the required information that you will need to configure the client computer?
Each correct answer represents a part of the solution. Choose two.
Joseph works as a Network Administrator for WebTech Inc. He has to set up a centralized area on the network so that each employee can share resources and documents with one another. Which of the following will he configure to accomplish the task?
Which of the following penetration testing phases involves gathering data from whois, DNS, and network scanning, which helps in mapping a target network and provides valuable information regarding the operating system and applications running on the systems?
Write the appropriate attack name to fill in the blank.
In a _____________ DoS attack, the attacker sends a spoofed TCP SYN packet in which the IP address of the target is filled in both the source and destination fields.
Analyze the output of the two commands below:
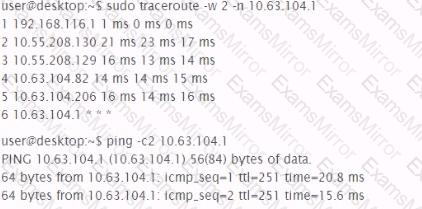
Which of the following can be factually inferred from the results of these commands?
You want to retrieve password files (stored in the Web server's index directory) from various Web sites. Which of the following tools can you use to accomplish the task?
TOP CODES
Top selling exam codes in the certification world, popular, in demand and updated to help you pass on the first try.
