Pre-Summer Special Limited Time 70% Discount Offer - Ends in 0d 00h 00m 00s - Coupon code = getmirror
Pass the GIAC Security Administration GPEN Questions and answers with ExamsMirror
Exam GPEN Premium Access
View all detail and faqs for the GPEN exam
742 Students Passed
93% Average Score
92% Same Questions
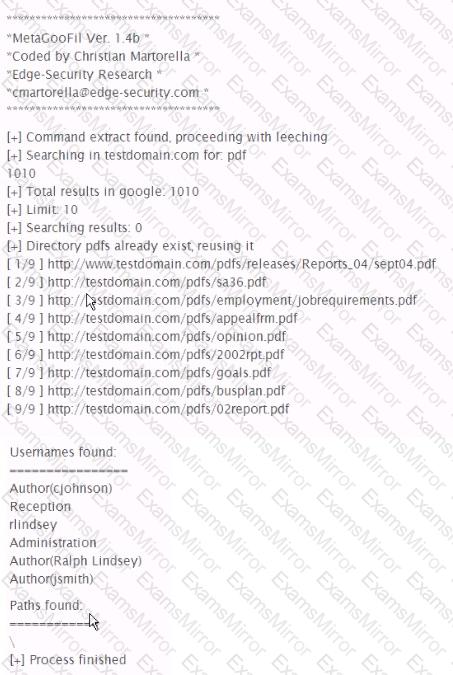
Analyze the command output below. What information can the tester infer directly from the Information shown?
While performing an assessment on a banking site, you discover the following link:
hnps://mybank.com/xfer.aspMer_toMaccount_number]&amount-[dollars]
Assuming authenticated banking users can be lured to your web site, which crafted html tag may be used to launch a XSRF attack?
Which Metasploitvncinject stager will allow VNC communications from the attacker to a listening port of the attacker's choosing on the victim machine?
Which of the following describes the direction of the challenges issued when establishing a wireless (IEEE 802.11) connection?
You have connected to a Windows system remotely and have shell access via netcat. While connected to the remote system you notice that some Windows commands work normally while others do not An example of this is shown in the picture below Which of the following best describes why tins is happening?

You are using the Nmap Scripting Engine and want detailed output of the script as it runs. Which option do you include in the command string?
You are conducting a penetration test for a private company located in Canada. The scope extends to all internal-facing hosts controlled by the company. You have gathered necessary hold-harmless and non-disclosure agreements. Which action by your group can incur criminal liability under Criminal Code of Canada Sections 184 and 542 CC 184?
When sniffing wireless frames, the interface mode plays a key role in successfully collecting traffic. Which of the mode or modes are best used for sniffing wireless traffic?
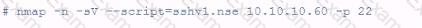
A customer has asked for a scan or vulnerable SSH servers. What is the penetration tester attempting to accomplish using the following Nmap command?
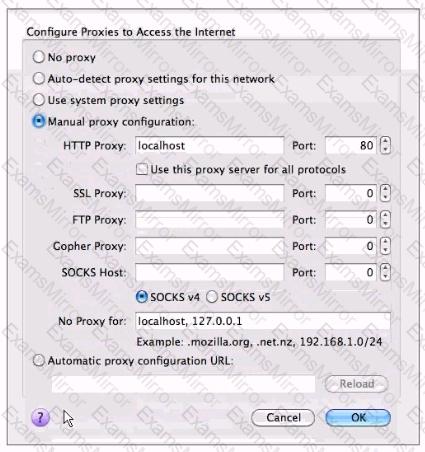
A junior penetration tester at your firm is using a non-transparent proxy for the first time to test a web server. He sees the web site In his browser but nothing shows up In the proxy. He tells you that he just installed the non-transparent proxy on his computer and didn't change any defaults. After verifying the proxy is running, you ask him to open up his browser configuration, as shown in the figure, which of the following recommendations will correctly allow him to use the transparent proxy with his browser?
TOP CODES
Top selling exam codes in the certification world, popular, in demand and updated to help you pass on the first try.
