Pre-Summer Special Limited Time 70% Discount Offer - Ends in 0d 00h 00m 00s - Coupon code = getmirror
Pass the GIAC Security Administration GPEN Questions and answers with ExamsMirror
Exam GPEN Premium Access
View all detail and faqs for the GPEN exam
742 Students Passed
93% Average Score
92% Same Questions
A penetration tester used a client-side browser exploit from metasploit to get an unprivileged shell prompt on the target Windows desktop. The penetration tester then tried using the getsystem command to perform a local privilege escalation which failed. Which of the following could resolve the problem?
How does OWASP ZAP function when used for performing web application assessments?
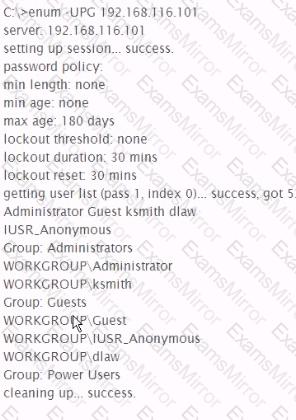
Analyze the command output below, what action is being performed by the tester?
Approximately how many packets are usually required to conduct a successful FMS attack onWEP?
A penetration tester obtains telnet access to a target machine using a captured credential. While trying to transfer her exploit to the target machine, the network intrusion detection systems keeps detecting her exploit and terminating her connection. Which of the following actions will help the penetration tester transfer an exploit and compile it in the target system?
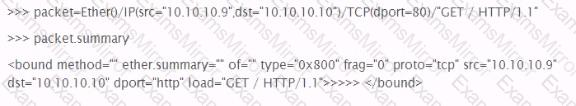
Given the following Scapy information, how is default Layer 2 information derived?
While performing a code audit, you discover a SQL injection vulnerability assuming the following vulnerable query, what user input could be injected to make the query true and return data?
select * from widgets where name = '[user-input]';
You successfully compromise a target system's web application using blind command injection. The command you injected is ping-n 1 192.168.1.200. Assuming your machine is 192.168.1 200, which of the following would you see?
What section of the penetration test or ethical hacking engagement final report is used to detail and prioritize the results of your testing?
You've been contracted by the owner of a secure facility to try and break into their office in the middle of the night. Your client requested photographs of any sensitive information found as proof of your accomplishments. The job you've been hired to perform is an example of what practice?
TOP CODES
Top selling exam codes in the certification world, popular, in demand and updated to help you pass on the first try.
