Pre-Summer Special Limited Time 70% Discount Offer - Ends in 0d 00h 00m 00s - Coupon code = getmirror
Pass the GIAC Security Administration GPEN Questions and answers with ExamsMirror
Exam GPEN Premium Access
View all detail and faqs for the GPEN exam
742 Students Passed
93% Average Score
92% Same Questions
Which of the following statements are true about the Enum tool?
Each correct answer represents a complete solution. Choose all that apply.
Adam is a novice Internet user. He is using Google search engine to search documents of his interest. Adam wants to search the text present in the link of a Website. Which of the following operators will he use in his query to accomplish the task?
You enter the following URL on your Web browser:
http://www.we-are-secure.com/scripts/..%co%af../..%co%
af../windows/system32/cmd.exe?/c+dir+c:\
What task do you want to perform?
Which of the following tools automates password guessing in the NetBIOS session?
Which of the following tools can be used to automate the MITM attack?
You work as a Penetration Tester for the Infosec Inc. Your company takes the projects of security auditing. Recently, your company has assigned you a project to test the security of the we-aresecure. com network. Now, when you have finished your penetration testing, you find that the weare- secure.com server is highly vulnerable to SNMP enumeration. You advise the we-are-secure Inc. to turn off SNMP; however, this is not possible as the company is using various SNMP services on its remote nodes. What other step can you suggest to remove SNMP vulnerability?
Each correct answer represents a complete solution. Choose two.
John works as a Professional Ethical Hacker for we-are-secure Inc. The company is using a Wireless network. John has been assigned the work to check the security of WLAN of we-aresecure.
For this, he tries to capture the traffic, however, he does not find a good traffic to analyze data. He has already discovered the network using the ettercap tool. Which of the following tools can he use to generate traffic so that he can crack the Wep keys and enter into the network?
Victor wants to use Wireless Zero Configuration (WZC) to establish a wireless network connection using his computer running on Windows XP operating system. Which of the following are the most likely threats to his computer?
Each correct answer represents a complete solution. Choose two.
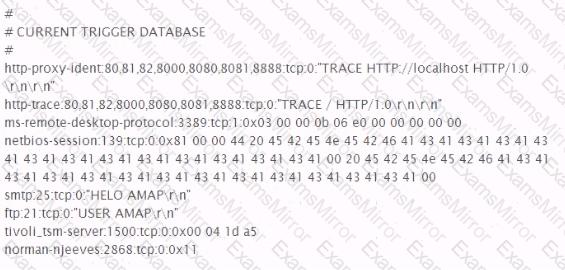
Based on the partial appdefstrig rile listed below, which port scan signature is classified by AMap as harmful?
What is the purpose of the following command?
C:\>wmic /node:[target IP] /user:[admin-user]
/password:[password] process call create [command]
TOP CODES
Top selling exam codes in the certification world, popular, in demand and updated to help you pass on the first try.
