Pre-Summer Special Limited Time 70% Discount Offer - Ends in 0d 00h 00m 00s - Coupon code = getmirror
Pass the GIAC Security Administration GPEN Questions and answers with ExamsMirror
Exam GPEN Premium Access
View all detail and faqs for the GPEN exam
742 Students Passed
93% Average Score
92% Same Questions
You want to search Microsoft Outlook Web Access Default Portal using Google search on the
Internet so that you can perform the brute force attack and get unauthorized access. What search string will you use to accomplish the task?
John works as a professional Ethical Hacker. He has been assigned the project of testing the security of www.we-are-secure.com. He is using a tool to crack the wireless encryption keys. The description of the tool is as follows:
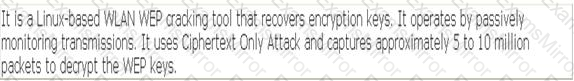
Which of the following tools is John using to crack the wireless encryption keys?
Which of the following is NOT a Back orifice plug-in?
Which of the following tools is used for SNMP enumeration?
Which of the following is the correct sequence of packets to perform the 3-way handshake method?
TOP CODES
Top selling exam codes in the certification world, popular, in demand and updated to help you pass on the first try.
