Pre-Summer Special Limited Time 70% Discount Offer - Ends in 0d 00h 00m 00s - Coupon code = getmirror
Pass the GIAC Security Administration GSEC Questions and answers with ExamsMirror
Exam GSEC Premium Access
View all detail and faqs for the GSEC exam
746 Students Passed
89% Average Score
94% Same Questions
While building multiple virtual machines on a single host operating system, you have determined that each virtual machine needs to work on the network as a separate entity with its own unique IP address on the same logical subnet. You also need to limit each guest operating system to how much system resources it has access to. Which of the following correctly identifies steps that must be taken towards setting up these virtual environments?
Which of the following features of Windows 7 allows an administrator to both passively review installed software and configure policies to prevent out-of-date or insecure software from running?
In PKI, when someone wants to verify that the certificate is valid, what do they use to decrypt the signature?
To update from a Windows Server Update Services (WSUS) server, users of the machine must have what rights, If any?
Which of the following hardware devices prevents broadcasts from crossing over subnets?
Which Authenticates Assurance Level requires a hardware-based authenticates?
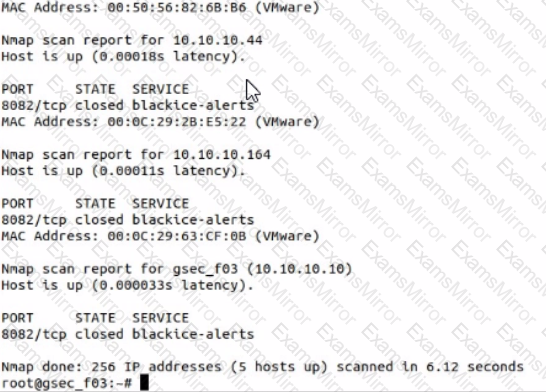
Use nmap to discover a host on the 10.10.10.0/24 network, scanning only port 8082 and using the SYN or Stealth scan approach. Which host has a service called -blackice-alerts"?

When a host on a remote network performs a DNS lookup of www.google.com, which of the following is likely to provide an Authoritative reply?
You are responsible for technical support at a company. One of the employees complains that his new laptop cannot connect to the company wireless network. You have verified that he is entering a valid password/passkey. What is the most likely problem?
John works as a Network Administrator for Perfect Solutions Inc. The company has a Linux-based network. John is working as a root user on the Linux operating system. He is currently working on his C based new traceroute program. Since, many processes are running together on the system, he wants to give the highest priority to the cc command process so that he can test his program, remove bugs, and submit it to the office in time. Which of the following commands will John use to give the highest priority to the cc command process?
TOP CODES
Top selling exam codes in the certification world, popular, in demand and updated to help you pass on the first try.
