Pre-Summer Special Limited Time 70% Discount Offer - Ends in 0d 00h 00m 00s - Coupon code = getmirror
Pass the GIAC Security Administration GSEC Questions and answers with ExamsMirror
Exam GSEC Premium Access
View all detail and faqs for the GSEC exam
746 Students Passed
89% Average Score
94% Same Questions
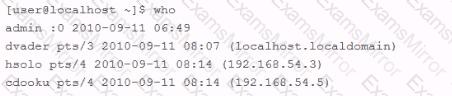
An employee is currently logged into the corporate web server, without permission. You log into the web server as 'admin" and look for the employee's username: "dmaul" using the "who" command. This is what you get back:
Which of the following works at the network layer and hides the local area network IP address and topology?
What is the key difference between Electronic Codebook mode and other block cipher modes like Cipher Block Chaining, Cipher-Feedback and Output-Feedback?
Which of the following is a signature-based intrusion detection system (IDS) ?
How is confidentiality disabled in the IPSec Encapsulated Security Payload protocol?
An organization monitors the hard disks of its employees' computers from time to time. Which policy does this pertain to?
Which of the following groups represents the most likely source of an asset loss through the inappropriate use of computers?
John works as a professional Ethical Hacker. He is assigned a project to test the security of www.we- are-secure.com. He installs a rootkit on the Linux server of the We-are-secure network. Which of the following statements are true about rootkits?
Each correct answer represents a complete solution. Choose all that apply.
What is it called when an OSI layer adds a new header to a packet?
What is the main problem with relying solely on firewalls to protect your company's sensitive data?
TOP CODES
Top selling exam codes in the certification world, popular, in demand and updated to help you pass on the first try.
