Pre-Summer Special Limited Time 70% Discount Offer - Ends in 0d 00h 00m 00s - Coupon code = getmirror
Pass the GIAC Security Administration GSEC Questions and answers with ExamsMirror
Exam GSEC Premium Access
View all detail and faqs for the GSEC exam
746 Students Passed
89% Average Score
94% Same Questions
Which of the following is NOT typically used to mitigate the war dialing threat?
What is log, pre-processing?
What is the purpose of notifying stakeholders prior to a scheduled vulnerability scan?
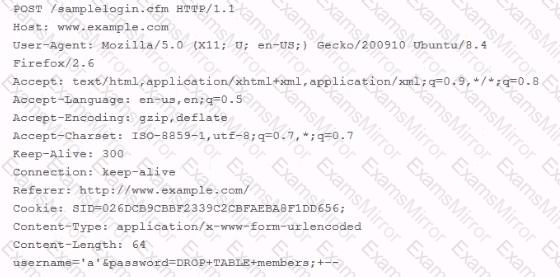
While using Wire shark to investigate complaints of users being unable to login to a web application, you come across an HTTP POST submitted through your web application. The contents of the POST are listed below. Based on what you see below, which of the following would you recommend to prevent future damage to your database?
What is the main reason that DES is faster than RSA?
Which of the following are used to suppress gasoline and oil fires? Each correct answer represents a complete solution. Choose three.
What is a recommended defense against SQL injection, OS injection, and buffer overflows?
When you log into your Windows desktop what information does your Security Access Token (SAT) contain?
What does the "x" character in the second field of the user account record of the /etc/passwd file indicate?
How many bytes does it take to represent the hexadecimal value OxFEDCBA?
TOP CODES
Top selling exam codes in the certification world, popular, in demand and updated to help you pass on the first try.
