Pre-Summer Special Limited Time 70% Discount Offer - Ends in 0d 00h 00m 00s - Coupon code = getmirror
Pass the GIAC Security Administration GSEC Questions and answers with ExamsMirror
Exam GSEC Premium Access
View all detail and faqs for the GSEC exam
746 Students Passed
89% Average Score
94% Same Questions
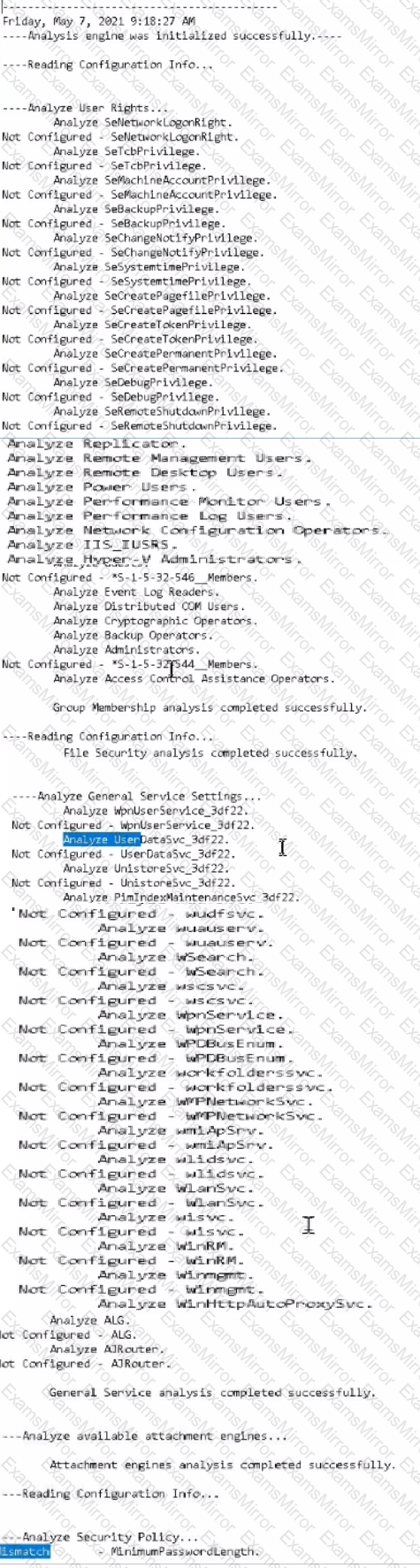
Using PowerShell ISE running as an Administrator, navigate to the
C:\hlindows\security\tevplatesdirectory. Use secedit.exe in analyze mode to compare the temp.sdb and uorkstdtionSecureTmplate.inf files, and output the findings to a file called log.txt. Which configuration setting under Analyze User Rights reports a mismatch?
Hints:
Use files located in the C \windows\security\templates\ directory
The log. txt file will be created in the directory the secedit.exe command is run from

Which access control mechanism requires a high amount of maintenance since all data must be classified, and all users granted appropriate clearance?
What type of formal document would include the following statement?
Employees are responsible for exercising good judgment regarding the reasonableness of personal use. Individual departments are responsible for creating guidelines concerning personal application of Internet/Intranet/Extranet systems. In the absence of such policies, employees should be guided by departmental policies, and if there is any uncertainty, employees should consult their supervisor or manager.
Which of the following radio frequencies is used by the IEEE 802.11a wireless network?
What is the motivation behind SYN/FIN scanning?
IPS devices that are classified as "In-line NIDS" devices use a combination of anomaly analysis, signature-based rules, and what else to identify malicious events on the network?
Which of the following types of computers is used for attracting potential intruders?
You work as a Network Administrator for Tech Perfect Inc. The company has a TCP/IP-based network. You have configured a firewall on the network. A filter has been applied to block all the ports. You want to enable sending and receiving of emails on the network. Which of the following ports will you open?
Each correct answer represents a complete solution. Choose two.
Which of the following classes of fire comes under Class C fire?
What is the maximum number of connections a normal Bluetooth device can handle at one time?
TOP CODES
Top selling exam codes in the certification world, popular, in demand and updated to help you pass on the first try.
