Pre-Summer Special Limited Time 70% Discount Offer - Ends in 0d 00h 00m 00s - Coupon code = getmirror
Pass the GIAC Management GSLC Questions and answers with ExamsMirror
Exam GSLC Premium Access
View all detail and faqs for the GSLC exam
785 Students Passed
86% Average Score
94% Same Questions
Which of the following types of firewall ensures that the packets are part of the established session?
Which of the following security protocols can be used to support MS-CHAPv2 for wireless client authentication?
Each correct answer represents a complete solution. Choose two.
In which of the following social engineering attacks does an attacker first damage any part of the target's equipment and then advertise himself as an authorized person who can help fix the problem.
A management workstation collects and connects events from multiple IPS sensors in the network.
Which protocol is used in this process?
Which of the following tasks can be performed by a malicious bot/botnet?
Each correct answer represents a complete solution. Choose all that apply.
Ned is the program manager for his organization and he's considering some new materials for his program. He and his team have never worked with these materials before and he wants to ask the vendor for some additional information, a demon, and even some samples. What type of a document should Ned send to the vendor?
Mark works as a Network Administrator for NetTech Inc. The company has a Windows 2003 Active Directory domain-based network. The domain consists of two Windows 2003 member servers and 500 Windows XP Professional client computers. The member servers are working as file servers. All the member servers are located in an OU named MEMSERV. Mark wants to test IPSec interoperability on the network. For this purpose, he creates a GPO named EXP. In the EXP GPO, he creates an IPSec policy named IPTEST. The IPTEST policy contains a rule that specifies the use of Encapsulating Security Payload (ESP) with null encryption. The IPTEST policy is applied to the member servers by linking the EXP GPO to the MEMSERV OU. After testing the IPSec interoperability, Mark wants to ensure that the member servers no longer use the IPTEST policy. What will he do to accomplish the task?
Which of the following functions can you use to mitigate a command injection attack?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following techniques is based on a set of criteria that has been acquired in a specific knowledge area or product area?
Your customer wants the fastest wireless possible in his home. Which of the following would you recommend?
Which of the following programs can be used to detect stealth port scans performed by a malicious hacker?
Each correct answer represents a complete solution. Choose all that apply.
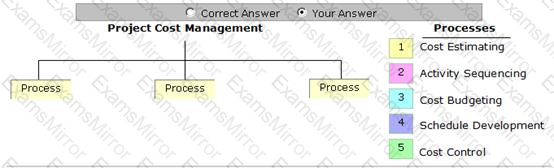
Place the processes that are grouped under the Project Cost Management Knowledge Area in the image below.
When no anomaly is present in an Intrusion Detection, but an alarm is generated, the response is known as __________.
Which of the following tools can be used to perform polymorphic shell code attacks?
Joseph works as a Network Administrator for WebTech Inc. He has to set up a centralized area on the network so that each employee can share resources and documents with one another. Which of the following will he configure to accomplish the task?
TOP CODES
Top selling exam codes in the certification world, popular, in demand and updated to help you pass on the first try.
