Pre-Summer Special Limited Time 70% Discount Offer - Ends in 0d 00h 00m 00s - Coupon code = getmirror
Pass the GIAC Management GSLC Questions and answers with ExamsMirror
Exam GSLC Premium Access
View all detail and faqs for the GSLC exam
785 Students Passed
86% Average Score
94% Same Questions
Which of the following is the method of hiding data within another media type such as graphic or document?
You work as a Network Administrator for PassGuide Inc. You have been assigned a task to provide the right authentications to users. Which method that uses a KDC will you use to accomplish the task?
Which of the following U.S. Federal laws addresses computer crime activities in communication lines, stations, or systems?
Fill in the blank with the appropriate term.
____________is a configuration of a network card that makes the card pass all traffic it receives to the central processing unit rather than just packets addressed to it.
Donna, a stakeholder in your project to create new software, has approached you about adding some features to the software package. You instruct that Donna must document the change request for it to be considered for the project. Why is it important for Donna to document the change request?
Which of the following are based on malicious code?
Each correct answer represents a complete solution. Choose two.
Which of the following tools is used to hide secret data in text files and is based on the concept that spaces and tabs are generally not visible in text viewers and therefore a message can be effectively hidden without affecting the text's visual representation for the casual observer?
Which of the following attacks is any form of cryptanalysis where the attacker can observe the operation of a cipher under several different keys whose values are initially unknown, but where some mathematical relationship connecting the keys is known to the attacker?
IP blocking is a technique that prevents the connection between a server/website and certain IP addresses or ranges of addresses. Which of the following tools use this technique?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following statements are true about locating rogue access points using WLAN discovery software such as NetStumbler, Kismet, or MacStumbler if you are using a Laptop integrated with Wi-Fi compliant MiniPCI card?
Each correct answer represents a complete solution. Choose two.
Managerial wisdom is the combination of knowledge as well as experience. It is the ability of the leaders to understand the members of the team. Which of the following are the characteristics that come under managerial wisdom?
Each correct answer represents a complete solution. Choose all that apply.
You work as a Network Administrator for Tech Perfect Inc. The company has a Windows Active Directory-based single domain single forest network. The functional level of the forest is Windows Server 2003. The company's headquarters is located at Los Angeles. A branch office of the company is located at Denver. You are about to send a message to Rick who is a Network Administrator at Denver. You want to ensure that the message cannot be read by anyone but the recipient. Which of the following keys will you use to encrypt the message?
You are the project manager of the Workstation Improvement Project for your organization. This project will replace 925 workstations with new computers for your company's employees. Mark Jones, the sales manager, has requested that your project add 250 laptops as part of this project as his employees do not have workstations as they travel as part of the sales process. Mark insists that his department in the company can pay for the cost of the laptops. All of the following are components that will be affected by this change request except for which one?
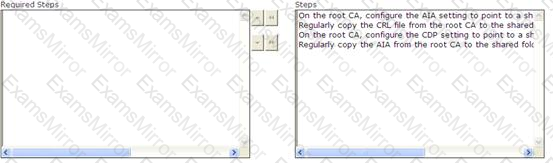
You work as a Network Administrator for Net World International. The company has a Windows Active Directory-based single domain single forest network. The functional level of the forest is Windows Server 2003. All client computers on the network run Windows XP Professional.
You configure a public key infrastructure (PKI) on the network. You configure a root CA and a subordinate CA on the network. For security reasons, you want to take the root CA offline. You are required to configure the CA servers to support for certificate revocation. Choose the steps you will require to accomplish the task.
You are concerned about rogue wireless access points being connected to your network. What is the best way to detect and prevent these?
TOP CODES
Top selling exam codes in the certification world, popular, in demand and updated to help you pass on the first try.
