Pre-Summer Special Limited Time 70% Discount Offer - Ends in 0d 00h 00m 00s - Coupon code = getmirror
Pass the GIAC Management GSLC Questions and answers with ExamsMirror
Exam GSLC Premium Access
View all detail and faqs for the GSLC exam
785 Students Passed
86% Average Score
94% Same Questions
Which of the following techniques is based on a set of criteria that has been acquired in a specific knowledge area or product area?
Which of the following evidences are the collection of facts that, when considered together, can be used to infer a conclusion about the malicious activity/person?
You work as a technician for Secure Net Inc. You receive an e-mail from your software vendor.
The e-mail contains information about a critical fix that needs to be installed on your computer. It further states that if this patch is not installed right away, your system will crash and you will lose all your data. Now they require your maintenance account password.
Which of the following types of security attacks do you think it is?
Which of the following viruses masks itself from applications or utilities to hide itself by detection of anti-virus software?
An Active Attack is a type of steganography attack in which the attacker changes the carrier during the communication process. Which of the following techniques is used for smoothing the transition and controlling contrast on the hard edges, where there is significant color transition?
Tim is working as a project manager for the TCH project. The project is in the final stages and the closing processes are being performed. He has prepared the lessons learned document. This document will be the part of ____.
Which of the following would allow you to automatically close connections or restart a server or service when a DoS attack is detected?
John works as a professional Ethical Hacker. He has been assigned the project of testing the security of www.we-are-secure.com. He receives the following e-mail:
The e-mail that John has received is an example of __________.
Which of the following work as traffic monitoring tools in the Linux operating system?
Each correct answer represents a complete solution. Choose two.
Which of the following options is an approach to restricting system access to authorized users?
You work as a Network Administrator for Tech Perfect Inc. The company has a Windows Server 2008 Active Directory-based single domain single forest network. The functional level of the forest is Windows Server 2008. The company's headquarters is located at Los Angeles. A branch office of the company is located at Denver. You are about to send a message to Rick who is a Network Administrator at Denver. You want to ensure that the message cannot be read by anyone but the recipient. Which of the following keys will you use to encrypt the message?
Which of the following is a signature-based intrusion detection system (IDS) ?
You work as an Incident handling manager for Orangesect Inc. You detect a virus attack incident in the network of your company. You develop a signature based on the characteristics of the detected virus. Which of the following phases in the Incident handling process will utilize the signature to resolve this incident?
Consider the following diagram:
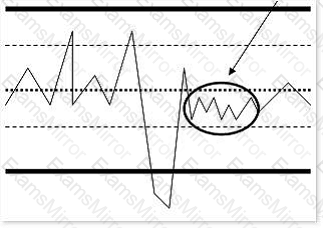
What is the highlighted area of the diagram known as?
Which of the following attacks allows the bypassing of access control lists on servers or routers, and helps an attacker to hide?
Each correct answer represents a complete solution. Choose two.
TOP CODES
Top selling exam codes in the certification world, popular, in demand and updated to help you pass on the first try.
