Pre-Summer Special Limited Time 70% Discount Offer - Ends in 0d 00h 00m 00s - Coupon code = getmirror
Pass the GIAC Management GSLC Questions and answers with ExamsMirror
Exam GSLC Premium Access
View all detail and faqs for the GSLC exam
785 Students Passed
86% Average Score
94% Same Questions
Which of the following is a network protocol that allows data to be exchanged using a secure channel between two networked devices?
John works as a professional Ethical Hacker. He has been assigned the project of testing the security of www.we-are-secure.com. He writes the following snort rule:
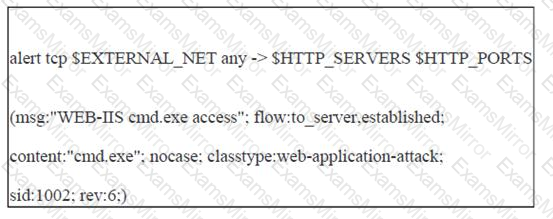
This rule can help him protect the We-are-secure server from the __________.
Andrew works as a Network Administrator for Infonet Inc. The company's network has a Web server that hosts the company's Web site. Andrew wants to increase the security of the Web site by implementing Secure Sockets Layer (SSL). Which of the following types of encryption does SSL use?
Each correct answer represents a complete solution. Choose two.
Which of the following is a type of encryption that uses a single key to encrypt and decrypt data?
Which of the following viruses replaces the boot sector data with its own malicious code?
Which of the following viruses infects Word 97 documents and the NORMAL.DOT file of Word 97 and Word 2000?
All of the following steps should be taken to prevent a Web server from IIS buffer overflow attacks except for which one?
Which of the following is a popular replacement for halon gas?
Which of the following attacks allows an attacker to recover the key in an RC4 encrypted stream from a large number of messages in that stream?
Which of the following attacks can be performed by Brutus for cracking a password?
Each correct answer represents a complete solution. Choose two.
You have inserted a Trojan on your friend's computer and you want to put it in the startup so that whenever the computer reboots the Trojan will start to run on the startup. Which of the following registry entries will you edit to accomplish the task?
Which of the following security policies will you implement to keep safe your data when you connect your Laptop to the office network over IEEE 802.11 WLANs?
Each correct answer represents a complete solution. Choose two.
You are responsible for securing the network at a law firm. They are particularly interested in ensuring that sensitive documents are not disclosed to outside parties. In securing the printers and scanners, which of the following statements are true?
Each correct answer represents a complete solution. Choose three.
Which of the following tools can be used for steganography?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following terms describes an attempt to transfer DNS zone data?
TOP CODES
Top selling exam codes in the certification world, popular, in demand and updated to help you pass on the first try.
