Pre-Summer Special Limited Time 70% Discount Offer - Ends in 0d 00h 00m 00s - Coupon code = getmirror
Pass the GIAC Security Administration GCIA Questions and answers with ExamsMirror
Exam GCIA Premium Access
View all detail and faqs for the GCIA exam
725 Students Passed
89% Average Score
93% Same Questions
Which of the following algorithms is used as a default algorithm for ESP extension header in IPv6?
What is the maximum size of an IP datagram for Ethernet?
You work as a desktop administrator for BlueSkwer.com. You are logged on to a Windows 7 computer with administrator rights. You have run the 'netsh interface IPv6 show interface' command which displays the following:
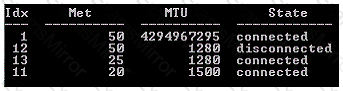
What is the first interface index used for?
Which of the following ports is used by e-mail clients to send request to connect to the server?
Victor wants to use Wireless Zero Configuration (WZC) to establish a wireless network connection using his computer running on Windows XP operating system. Which of the following are the most likely threats to his computer?
Each correct answer represents a complete solution. Choose two.
Which of the following groups provides tools and creates procedures for testing and validating computer forensic software?
You work as a Network Administrator for Net Perfect Inc. The company has a TCP/IP-based network. The network is connected to the Internet through a firewall. A user complains that he is unable to access the abc.com site. However, he can access all other sites. Which of the following tools will help you diagnose the problem?
Which of the following cryptographic methods are used in EnCase to ensure the integrity of the data, which is acquired for the investigation?
Each correct answer represents a complete solution. Choose two.
Adam works as a professional Computer Hacking Forensic Investigator. A project has been assigned to him to investigate a multimedia enabled mobile phone, which is suspected to be used in a cyber crime. Adam uses a tool, with the help of which he can recover deleted text messages, photos, and call logs of the mobile phone. Which of the following tools is Adam using?
Fill in the blank with the appropriate facts regarding IP version 6 (IPv6).
IP addressing version 6 uses_____ -bit address. Its____ IP address assigned to a single host allows the host to send and receive data.
Which of the following components are usually found in an Intrusion detection system (IDS)?
Each correct answer represents a complete solution. Choose two.
Which of the following algorithms is used as a default algorithm for ESP extension header in IPv6?
At which layers of the OSI and TCP/IP models does IP addressing function?
You are the Network Administrator for a large corporate network. You want to monitor all network traffic on your local network for suspicious activities and receive a notification when a possible attack is in process. Which of the following actions will you take for this?
Mark has been assigned a project to configure a wireless network for a company. The network should contain a Windows 2003 server and 30 Windows XP client computers. Mark has a single dedicated Internet connection that has to be shared among all the client computers and the server. The configuration needs to be done in a manner that the server should act as a proxy server for the client computers. Which of the following programs can Mark use to fulfill this requirement?
TOP CODES
Top selling exam codes in the certification world, popular, in demand and updated to help you pass on the first try.
