Pre-Summer Special Limited Time 70% Discount Offer - Ends in 0d 00h 00m 00s - Coupon code = getmirror
Pass the GIAC Security Administration GCIA Questions and answers with ExamsMirror
Exam GCIA Premium Access
View all detail and faqs for the GCIA exam
725 Students Passed
89% Average Score
93% Same Questions
Which of the following is the correct order of digital investigations Standard Operating Procedure (SOP)?
You work as a Network Administrator for Net Perfect Inc. The company has a TCP/IP-based network. You are configuring an Internet connection on a server. Which of the following servers filters outbound Web traffic on the network?
Which of the following statements are true about snort?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following tools is used to detect wireless LANs using the 802.11b, 802.11a, and 802.11g WLAN standards on the Windows platform?
You work as a Desktop Support Technician for umbrella Inc. The company uses a Windows-based network. An employee of the production department is facing the problem in the IP configuration of the network connection.
He called you to resolve the issue. You suspect that the IP configuration is not configured properly. You want to use the ping command to ensure that IPv4 protocol is working on a computer. While running the ping command from the command prompt, you find that Windows Firewall is blocking the ping command. You enter the following command in the elevated command prompt on the computer:
netsh advfirewall firewall add rule name="ICMPv4" protocol=icmpv4:any,any dir=in action=allow
Which of the following actions will this command perform?
Which of the following is the default port for Simple Network Management Protocol (SNMP)?
John works as a Network Administrator for DigiNet Inc. He wants to investigate failed logon attempts to a network. He uses Log Parser to detail out the failed logons over a specific time frame. He uses the following commands and query to list all failed logons on a specific date:
logparser.exe file:FailedLogons.sql -i:EVT -o:datagrid
SELECT
timegenerated AS LogonTime,
extract_token(strings, 0, '|') AS UserName
FROM Security
WHERE EventID IN (529;
530;
531;
532;
533;
534;
535;
537;
539)
AND to_string(timegenerated,'yyyy-MM-dd HH:mm:ss') like '2004-09%'
After investigation, John concludes that two logon attempts were made by using an expired account. Which of the following EventID refers to this failed logon?
Which of the following is known as a message digest?
Every network device contains a unique built in Media Access Control (MAC) address, which is used to identify the authentic device to limit the network access. Which of the following addresses is a valid MAC address?
Which of the following is included in a memory dump file?
Which of the following file systems is designed by Sun Microsystems?
You work as a Network Security Analyzer. You got a suspicious email while working on a forensic project. Now, you want to know the IP address of the sender so that you can analyze various information such as the actual location, domain information, operating system being used, contact information, etc. of the email sender with the help of various tools and resources. You also want to check whether this email is fake or real. You know that analysis of email headers is a good starting point in such cases. The email header of the suspicious email is given below:
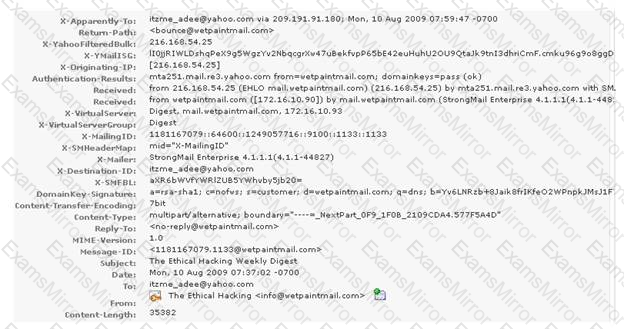
What is the IP address of the sender of this email?
You work as a System Administrator for McNeil Inc. The company has a Linux-based network. You are a root user on the Red Hat operating system. Your network is configured for IPv6 IP addressing. Which of the following commands will you use to test TCP/IP connectivity?
A firewall is a combination of hardware and software, used to provide security to a network. It is used to protect an internal network or intranet against unauthorized access from the Internet or other outside networks. It restricts inbound and outbound access and can analyze all traffic between an internal network and the Internet. Users can configure a firewall to pass or block packets from specific IP addresses and ports. Which of the following tools works as a firewall for the Linux 2.4 kernel?
Which of the following tools is described below?
It is a set of tools that are used for sniffing passwords, e-mail, and HTTP traffic. Some of its tools include arpredirect, macof, tcpkill, tcpnice, filesnarf, and mailsnarf. It is highly effective for sniffing both switched and shared networks. It uses the arpredirect and macof tools for switching across switched networks. It can also be used to capture authentication information for FTP, telnet, SMTP, HTTP, POP, NNTP, IMAP, etc.
TOP CODES
Top selling exam codes in the certification world, popular, in demand and updated to help you pass on the first try.
