Pre-Summer Special Limited Time 70% Discount Offer - Ends in 0d 00h 00m 00s - Coupon code = getmirror
Pass the GIAC Security Administration GCIA Questions and answers with ExamsMirror
Exam GCIA Premium Access
View all detail and faqs for the GCIA exam
725 Students Passed
89% Average Score
93% Same Questions
The following output is generated by running the show ip route command:
RouterA#show ip route
< - - Output Omitted for brevity - ->
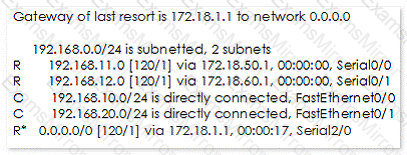
Which next hop address will RouterA use in forwarding traffic to 10.10.100.0/24?
Which of the following proxy servers is placed anonymously between the client and remote server and handles all of the traffic from the client?
Which of the following commands will you use with the tcpdump command to capture the traffic from a filter stored in a file?
Which of the following is allowed by a company to be addressed directly from the public network and is hardened to screen the rest of its network from security exposure?
Which of the following tools works by using standard set of MS-DOS commands and can create an MD5 hash of an entire drive, partition, or selected files?
Which of the following statements best describes the string matching method of signature analysis?
What are the advantages of an application layer firewall?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following units of data does the data-link layer send from the network layer to the physical layer of the OSI model?
Adam works as a professional Computer Hacking Forensic Investigator. A project has been assigned to him to investigate computer of an unfaithful employee of SecureEnet Inc. Suspect's computer runs on Windows operating system. Which of the following sources will Adam investigate on a Windows host to collect the electronic evidences?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following attacks is used to hack simple alphabetical passwords?
Which of the following NETSH commands for interface Internet protocol version 4 (IPv4) is used to delete a DNS server or all DNS servers from a list of DNS servers for a specified interface or for all interfaces?
Which of the following firewalls depends on the three-way handshake of the TCP protocol?
Which of the following methods is used by forensic investigators to acquire an image over the network in a secure manner?
Which of the following commands is a Packet sniffer?
Which of the following TCP/UDP port is used by the toolkit program netstat?
TOP CODES
Top selling exam codes in the certification world, popular, in demand and updated to help you pass on the first try.
