Pre-Summer Special Limited Time 70% Discount Offer - Ends in 0d 00h 00m 00s - Coupon code = getmirror
Pass the GIAC Security Administration GCIA Questions and answers with ExamsMirror
Exam GCIA Premium Access
View all detail and faqs for the GCIA exam
725 Students Passed
89% Average Score
93% Same Questions
Which of the following utilities provides information as per the format given below?
Which of the following statements about FTP is true?
Adam, a malicious hacker is running a scan. Statistics of the scan is as follows:
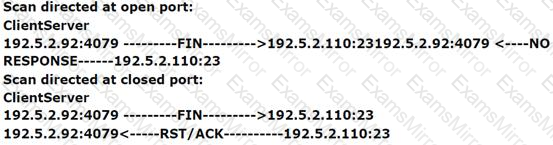
Which of the following types of port scan is Adam running?
Adam, a novice Web user is getting large amount of unsolicited commercial emails on his email address. He suspects that the emails he is receiving are the Spam. Which of the following steps will he take to stop the Spam?
Each correct answer represents a complete solution. Choose all that apply.
You are implementing a host based intrusion detection system on your web server. You feel that the best way to monitor the web server is to find your baseline of activity (connections, traffic, etc.) and to monitor for conditions above that baseline. This type of IDS is called __________.
Which of the following is the primary TCP/IP protocol used to transfer text and binary files over the Internet?
You are using a Windows-based sniffer named ASniffer to record the data traffic of a network. You have extracted the following IP Header information of a randomly chosen packet from the sniffer's log:
45 00 00 28 00 00 40 00 29 06 43 CB D2 D3 82 5A 3B 5E AA 72
Which of the following TTL decimal values and protocols are being carried by the IP Header of this packet?
What is the easiest way to verify that name resolution is functioning properly on a TCP/IP network?
Which of the following types of scan does not open a full TCP connection?
Which of the following is the process of categorizing attack alerts produced from an IDS in order to distinguish false positives from actual attacks?
Which of the following tools is used to store the contents of a TDB (Trivial Database) file to the standard output when debugging problems with TDB files?
Which of the following utilities provides an efficient way to give specific users permission to use specific system commands at the root level of a Linux operating system?
You work as a Network Administrator for NetTech Inc. You want to know the local IP address, subnet mask, and default gateway of a NIC in a Windows 98 computer. Which of the following utilities will you use to accomplish this ?
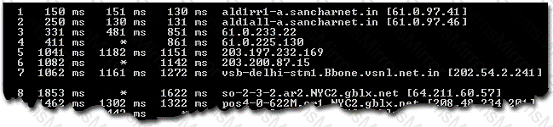
Which of the following utilities produces the output shown in the image below?

Which of the following are open-source vulnerability scanners?
TOP CODES
Top selling exam codes in the certification world, popular, in demand and updated to help you pass on the first try.
