Pre-Summer Special Limited Time 70% Discount Offer - Ends in 0d 00h 00m 00s - Coupon code = getmirror
Pass the GIAC Security Administration GCIA Questions and answers with ExamsMirror
Exam GCIA Premium Access
View all detail and faqs for the GCIA exam
725 Students Passed
89% Average Score
93% Same Questions
Which of the following standard file formats is used by Apple's iPod to store contact information?
Users on a TCP/IP network are able to ping resources using IP addresses. However, they are unable to connect to those resources through their host names. A malfunction or failure of which of the following servers may be the cause of the issue?
Which of the following work as traffic monitoring tools in the Linux operating system?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following can be configured so that when an alarm is activated, all doors lock and the suspect or intruder is caught between the doors in the dead-space?
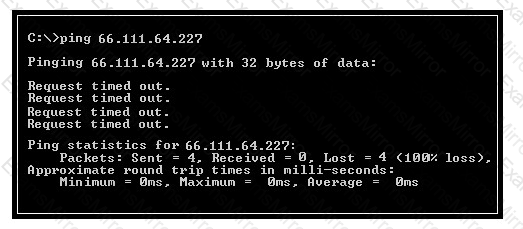
Which of the following conclusions can be drawn from viewing the given output generated by the PING command-line utility?
Nathan works as a professional Ethical Hacker. He wants to see all open TCP/IP and UDP ports of his computer. Nathan uses the netstat command for this purpose but he is still unable to map open ports to the running process with PID, process name, and path. Which of the following commands will Nathan use to accomplish the task?
Adam works as a Security Analyst for Umbrella Inc. He is performing real-time traffic analysis on IP networks using Snort. Adam is facing problems in analyzing intrusion data. Which of the following software combined with Snort can Adam use to get a visual representation of intrusion data?
Each correct answer represents a complete solution. Choose all that apply.
Andrew works as a System Administrator for NetPerfect Inc. All client computers on the network run on Mac OS X. The Sales Manager of the company complains that his MacBook is not able to boot. Andrew wants to check the booting process. He suspects that an error persists in the bootloader of Mac OS X. Which of the following is the default bootloader on Mac OS X that he should use to resolve the issue?
John works as a professional Ethical Hacker. He has been assigned a project to test the security of www.we-are-secure.com. John wants to redirect all TCP port 80 traffic to UDP port 40, so that he can bypass the firewall of the We-are-secure server. Which of the following tools will John use to accomplish his task?
Which of the following firewalls keeps track of the state of network connections traveling across the network?
Which of the following is a signature-based intrusion detection system (IDS) ?
You work as a Network Administrator for Net Perfect Inc. The company has a Windows Server
2008 network environment. The servers on the network run Windows Server 2008 R2. All client computers on the network run Windows 7 Ultimate. You have configured DirectAccess feature on the laptop of few sales managers so that they can access corporate network from remote locations. Their laptops run Windows 7 Ultimate. Which of the following options does the DirectAccess use to keep data safer while traveling through travels public networks?
Peter works as a Technical Representative in a CSIRT for SecureEnet Inc. His team is called to investigate the computer of an employee, who is suspected for classified data theft. Suspect's computer runs on Windows operating system. Peter wants to collect data and evidences for further analysis. He knows that in Windows operating system, the data is searched in pre-defined steps for proper and efficient analysis. Which of the following is the correct order for searching data on a Windows based system?
You work as a Network Administrator for Tech2tech Inc. You have configured a network-based IDS for your company.
You have physically installed sensors at all key positions throughout the network such that they all report to the command console.
What will be the key functions of the sensors in such a physical layout?
Each correct answer represents a complete solution. Choose all that apply.
Which of the following is the default port for File Transport Protocol (FTP)?
TOP CODES
Top selling exam codes in the certification world, popular, in demand and updated to help you pass on the first try.
